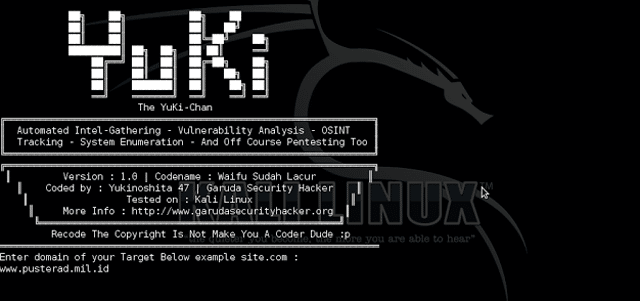
Yuki Chan is an Automated Penetration Testing Tool that carries out a whole range of standard security auditing tasks automatically. It’s highly recommended to use this tool within Kali Linux OS as it already contains all the dependencies.
This tool is only designed for Linux OS so if you are not using Linux OS it won’t be much use, but if you have Android Smartphone or Tablet you can run this tool via Termux or GNURoot Debian.
There are some other tools that attempt to string together popular hacking tools like Yuki Chan does to automate at least some part of the penetrating testing process such as:
– Sn1per – Penetration Testing Automation Scanner
– Fast-Track 4.0 – Automated Penetration Testing Suite
Features of Yuki Chan Automated Penetration Testing Tool
The standard functions performed by this tool out of the box are:
- Automated
- Intel Gathering
- Vulnerability Analysis
- Security Auditing
- OSINT
- Tracking
- System Enumeration
- Fuzzing
- CMS Auditing
- SSL Security Auditing
Modules in Yuki Chan for Automated Pen-Testing
- WHOIS domain analyzer
- NSlookup
- Nmap
- TheHarvester
- Metagoofil
- DNSRecon
- Sublist3r
- Wafw00f
- WAFNinja
- XSS Scanner
- WhatWeb
- Spaghetti
- WPscan
- WPscanner
- WPSeku
- Droopescan
- SSLScan
- SSLyze
- A2SV
- Dirsearch
You can download Yuki Chan for Automated Pen Testing here:
Yuki-Chan-The-Auto-Pentest-master.zip
Or read more here.
