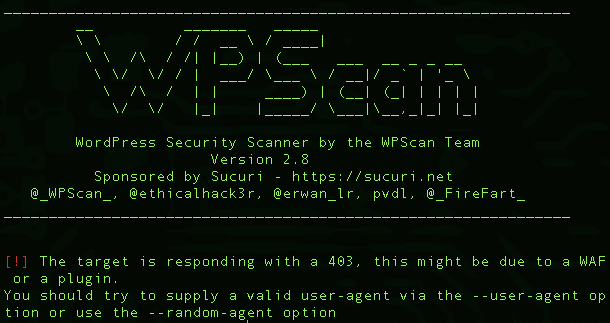
WPScan is a WordPress vulnerability scanner which checks the security of WordPress installations using a black box approach (scanning without any prior knowledge of what has been installed etc).
Features of WPScan WordPress Vulnerability Scanner
- Username enumeration (from author querystring and location header)
- Weak password cracking (multithreaded)
- Version enumeration (from generator meta tag)
- Vulnerability enumeration (based on version)
- Plugin enumeration (2220 most popular by default)
- Plugin vulnerability enumeration (based on version) (todo)
- Plugin enumeration list generation
- Other misc WordPress checks (theme name, dir listing, …)
WPScan Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 |
--update Update the database to the latest version. --url | -u <target url> The WordPress URL/domain to scan. --force | -f Forces WPScan to not check if the remote site is running WordPress. --enumerate | -e [option(s)] Enumeration. option : u usernames from id 1 to 10 u[10-20] usernames from id 10 to 20 (you must write [] chars) p plugins vp only vulnerable plugins ap all plugins (can take a long time) tt timthumbs t themes vt only vulnerable themes at all themes (can take a long time) Multiple values are allowed : "-e tt,p" will enumerate timthumbs and plugins If no option is supplied, the default is "vt,tt,u,vp" --exclude-content-based "<regexp or string>" Used with the enumeration option, will exclude all occurrences based on the regexp or string supplied. You do not need to provide the regexp delimiters, but you must write the quotes (simple or double). --config-file | -c <config file> Use the specified config file, see the example.conf.json. --user-agent | -a <User-Agent> Use the specified User-Agent. --cookie <string> String to read cookies from. --random-agent | -r Use a random User-Agent. --follow-redirection If the target url has a redirection, it will be followed without asking if you wanted to do so or not --batch Never ask for user input, use the default behaviour. --no-color Do not use colors in the output. --log [filename] Creates a log.txt file with WPScan's output if no filename is supplied. Otherwise the filename is used for logging. --no-banner Prevents the WPScan banner from being displayed. --disable-accept-header Prevents WPScan sending the Accept HTTP header. --disable-referer Prevents setting the Referer header. --disable-tls-checks Disables SSL/TLS certificate verification. --wp-content-dir <wp content dir> WPScan try to find the content directory (ie wp-content) by scanning the index page, however you can specify it. Subdirectories are allowed. --wp-plugins-dir <wp plugins dir> Same thing than --wp-content-dir but for the plugins directory. If not supplied, WPScan will use wp-content-dir/plugins. Subdirectories are allowed --proxy <[protocol://]host:port> Supply a proxy. HTTP, SOCKS4 SOCKS4A and SOCKS5 are supported. If no protocol is given (format host:port), HTTP will be used. --proxy-auth <username:password> Supply the proxy login credentials. --basic-auth <username:password> Set the HTTP Basic authentication. --wordlist | -w <wordlist> Supply a wordlist for the password brute forcer. If the "-" option is supplied, the wordlist is expected via STDIN. --username | -U <username> Only brute force the supplied username. --usernames <path-to-file> Only brute force the usernames from the file. --cache-dir <cache-directory> Set the cache directory. --cache-ttl <cache-ttl> Typhoeus cache TTL. --request-timeout <request-timeout> Request Timeout. --connect-timeout <connect-timeout> Connect Timeout. --threads | -t <number of threads> The number of threads to use when multi-threading requests. --max-threads <max-threads> Maximum Threads. --throttle <milliseconds> Milliseconds to wait before doing another web request. If used, the --threads should be set to 1. --help | -h This help screen. --verbose | -v Verbose output. --version Output the current version and exit. |
WPScan Requirements
The following are required for a manual (non-docker) install:
- Ruby >= 2.1.9 – Recommended: 2.4.1
- Curl >= 7.21 – Recommended: latest – FYI the 7.29 has a segfault
- RubyGems – Recommended: latest
- Git
|
1 |
sudo apt-get install libcurl4-openssl-dev libxml2 libxml2-dev libxslt1-dev ruby-dev build-essential libgmp-dev zlib1g-dev |
Manual installation with RVM
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
# Install all prerequisites for your OS (look above) cd ~ curl -sSL https://rvm.io/mpapis.asc | gpg --import - curl -sSL https://get.rvm.io | bash -s stable source ~/.rvm/scripts/rvm echo "source ~/.rvm/scripts/rvm" >> ~/.bashrc rvm install 2.4.1 rvm use 2.4.1 --default echo "gem: --no-ri --no-rdoc" > ~/.gemrc git clone https://github.com/wpscanteam/wpscan.git cd wpscan gem install bundler bundle install --without test |
You can download WPScan latest version here:
Or you can read more here.
