Sublist3r is a Python-based tool designed to enumerate subdomains of websites using OSINT. It helps penetration testers and bug hunters collect and gather subdomains for the domain they are targeting.
It also integrates with subbrute for subdomain brute-forcing with word lists.
Features of Sublist3r Subdomain Enumeration Tool
It enumerates subdomains using many search engines such as:
- Yahoo
- Bing
- Baidu
- Ask
The tool also enumerates subdomains using:
- Netcraft
- Virustotal
- ThreatCrowd
- DNSdumpster
- ReverseDNS
Requirements of Sublist3r Subdomain Search
It currently supports Python 2 and Python 3.
– The recommended version for Python 2 is 2.7.x
– The recommended version for Python 3 is 3.4.x
The tool depends on the requests, dnspython, and argparse Python modules.
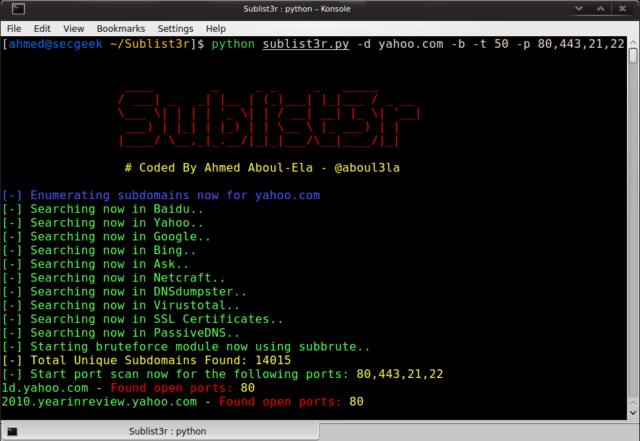
Usage of Sublist3r Subdomain Brute Force Tool
|
1 2 3 4 5 6 7 8 9 10 |
./sublist3r.py -h -d --domain Domain name to enumerate subdomains of -b --bruteforce Enable the subbrute bruteforce module -p --ports Scan the found subdomains against specific tcp ports -v --verbose Enable the verbose mode and display results in realtime -t --threads Number of threads to use for subbrute bruteforce -e --engines Specify a comma-separated list of search engines -o --output Save the results to text file -h -help show the help message and exit |
Examples
To list all the basic options and switches use -h switch:
|
1 |
python sublist3r.py -h |
To enumerate subdomains of specific domain:
|
1 |
python sublist3r.py -d example.com |
To enumerate subdomains of specific domain and show only subdomains which have open ports 80 and 443 :
|
1 |
python sublist3r.py -d example.com -p 80,443 |
To enumerate subdomains of specific domain and show the results in realtime:
|
1 |
python sublist3r.py -v -d example.com |
To enumerate subdomains and enable the bruteforce module:
|
1 |
python sublist3r.py -b -d example.com |
To enumerate subdomains and use specific engines such Google, Yahoo and Virustotal engines
|
1 |
python sublist3r.py -e google,yahoo,virustotal -d example.com |
It’s also possible to use Sublist3r as a Python module in your own scripts.
Other tools to check out are:
– SubBrute – Subdomain Brute-forcing Tool
– Knock v1.3b – Subdomain Enumeration/Brute-Forcing Tool
– DNSRecon – DNS Enumeration Script
– InstaRecon – Automated Subdomain Discovery Tool
You can download Sublist3r here:
Or read more here.
