AgentSmith HIDS is a powerful component of a Host-based Intrusion Detection system, it has anti-rootkit functionalities and is a very performant way to collect information about a host.
Technically, AgentSmith-HIDS is not a Host-based Intrusion Detection System (HIDS) due to a lack of a rule engine and detection function. However, it can be used as a high-performance ‘Host Information Collect Agent’ as part of your own HIDS solution. The comprehensiveness of information that this agent can collect was one of the most important metrics during development of this project, hence it was built to function in the kernel stack and achieve huge advantages compared to those functions in the user stack, such as:
- For better performance – Information needed is collected in the kernel stack to avoid additional supplement actions such as traversal of ‘/proc’; and to enhance the performance of data transportation, data collected is transferred via shared RAM instead of netlink.
- Hard to be bypassed – information collection was powered by a specifically designed kernel drive, making it almost impossible to bypass the detection of malicious software like rootkits, which can deliberately hide themselves.
- Easy to integrate – the AgentSmith-HIDS was built to integrate with other applications and can be used not only as a security tool but also as a good monitoring tool, or even a good detector of your assets. The agent can collect the users, files, processes and internet connections for you, so let’s imagine when you integrate it with CMDB, you could get a comprehensive map consisting of your network, host, container and business (even dependencies). What if you also have a Database audit tool at hand? The map can be extended to contain the relationship between your DB, DB User, tables, fields, applications, network, host containers etc. Thinking of the possibility of integration with network intrusion detection systems and/or threat intelligence etc., higher traceability could also be achieved. It just never gets old.
- Kernel stack + User stack – AgentSmith-HIDS also provide a user stack module, to further extend the functionality when working with a kernel stack module.
Feature of AgentSmith HIDS
- Kernel stack module hooks execve, connect, process inject, create file, DNS query, load LKM behaviors via Kprobe,and is also capable of monitoring containers by being compatible with Linux namespace.
- User stack module utilize built in detection functions including queries of User List,Listening ports list,System RPM list,Schedule jobs
- AntiRootkit,From: Tyton ,for now add PROC_FILE_HOOK,SYSCALL_HOOK,LKM_HIDDEN,INTERRUPTS_HOOK feature,but only wark on Kernel > 3.10.
- Cred Change monitoring (sudo/su/sshd except)
- User Login monitoring
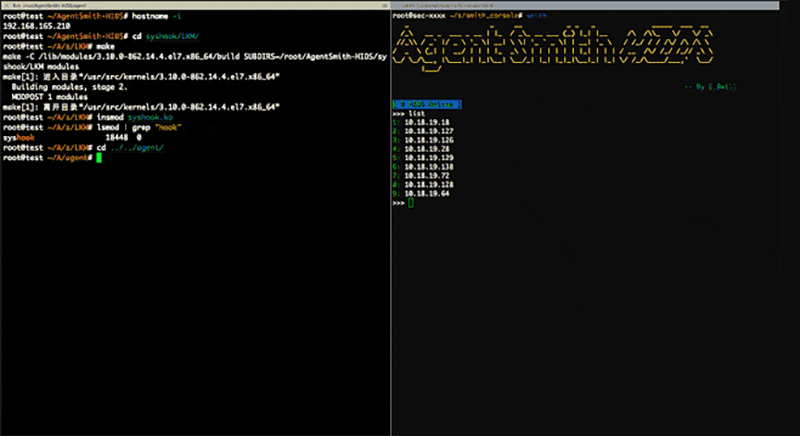
AgentSmith HIDS Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 |
{ "uid":"0", "data_type":"59", "run_path":"/tmp", "exe":"/opt/ltp/testcases/bin/growfiles", "argv":"growfiles -W gf26 -D 0 -b -i 0 -L 60 -u -B 1000b -e 1 -r 128-32768:128 -R 512-64000 -T 4 -f gfsmallio-35861 -d /tmp/ltp-Ujxl8kKsKY ", "pid":"35861", "ppid":"35711", "pgid":"35861", "tgid":"35861", "comm":"growfiles", "nodename":"test", "stdin":"/dev/pts/1", "stdout":"/dev/pts/1", "sessionid":"3", "sip":"192.168.165.1", "sport":"61726", "dip":"192.168.165.128", "dport":"22", "sa_family":"1", "pid_tree":"1(systemd)->1384(sshd)->2175(sshd)->2177(bash)->2193(fish)->35552(runltp)->35711(ltp-pan)->35861(growfiles)", "tty_name":"pts1", "socket_process_pid":"2175", "socket_process_exe":"/usr/sbin/sshd", "SSH_CONNECTION":"192.168.165.1 61726 192.168.165.128 22", "LD_PRELOAD":"/root/ldpreload/test.so", "user":"root", "time":"1579575429143", "local_ip":"192.168.165.128", "hostname":"test", "exe_md5":"01272152d4901fd3c2efacab5c0e38e5", "socket_process_exe_md5":"686cd72b4339da33bfb6fe8fb94a301f" } |
You can download AgentSmith here:
Or read more here.
