Vulhub is an open-source collection of pre-built vulnerable docker environments for learning to hack. No pre-existing knowledge of docker is required, just execute two simple commands and you have a vulnerable environment. Features of Vulhub Pre-Built Vulnerable Docker Environments For Learning To Hack Vulhub contains many frameworks, databases, applications, programming languages and more such as: […]
Exploits/Vulnerabilities
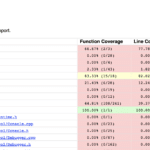
Fuzzilli – JavaScript Engine Fuzzing Library
Fuzzilii is a JavaScript engine fuzzing library, it’s a coverage-guided fuzzer for dynamic language interpreters based on a custom intermediate language (“FuzzIL”) which can be mutated and translated to JavaScript. When fuzzing for core interpreter bugs, e.g. in JIT compilers, semantic correctness of generated programs becomes a concern. This is in contrast to most other […]
Four Year Old libssh Bug Leaves Servers Wide Open
A fairly serious 4-year old libssh bug has left servers vulnerable to remote compromise, fortunately, the attack surface isn’t that big as neither OpenSSH or the GitHub implementation are affected. The bug is in the not so widely used libSSH library, not to be confused with libssh2 or OpenSSH – which are very widely used. […]
SCADA Hacking – Industrial Systems Woefully Insecure
It seems like SCADA hacking is still a topic in hacker conferences, and it should be with SCADA systems still driving power stations, manufacturing plants, refineries and all kinds of other powerful and dangerous things. The latest talk given on the subject shows with just 4 lines of code and a small hardware drop device […]
XXE Injection Attacks – XML External Entity Vulnerability With Examples
XXE Injection Attacks or XML External Entity vulnerabilities are a specific type of Server Side Request Forgery or SSRF attack relating to abusing features within XML parsers. The features these attacks go after are widely available but rarely used and when trigged can cause a DoS (Denial of Service) attack and in some cases much […]