WhatWeb identifies websites. Its goal is to answer the question, “What is that Website?”. WhatWeb recognises web technologies including content management systems (CMS), blogging platforms, statistic/analytics packages, JavaScript libraries, web servers, and embedded devices. WhatWeb has over 1500 plugins, each to recognise something different. WhatWeb also identifies version numbers, email addresses, account IDs, web framework modules, SQL errors, and more.
What is WhatWeb?
WhatWeb can be stealthy and fast, or thorough but slow. WhatWeb supports an aggression level to control the tradeoff between speed and reliability. When you visit a website in your browser, the transaction includes many hints of what web technologies are powering that website. Sometimes a single webpage visit contains enough information to identify a website but when it does not, WhatWeb can interrogate the website further. The default level of aggression, called ‘stealthy’, is the fastest and requires only one HTTP request of a website. This is suitable for scanning public websites. More aggressive modes were developed for use in penetration tests.
Most WhatWeb plugins are thorough and recognise a range of cues from subtle to obvious. For example, most WordPress websites can be identified by the meta HTML tag, e.g. meta name="generator" content="WordPress 2.6.5", but a minority of WordPress websites remove this identifying tag but this does not thwart WhatWeb. The WordPress WhatWeb plugin has over 15 tests, which include checking the favicon, default installation files, login pages, and checking for “/wp-content/” within relative links.
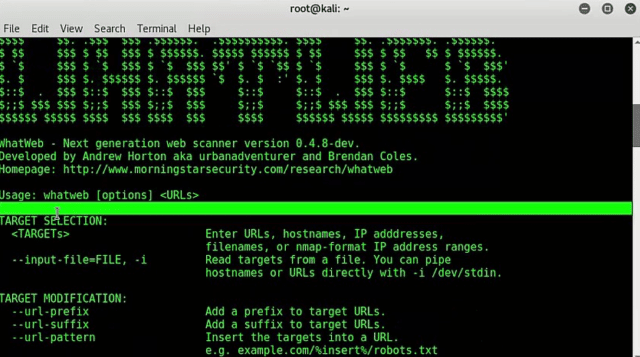
We wrote about WhatWeb way back in 2010, and there actually hasn’t been a release since 2011 (v0.4.7). I was glad to find however it still is under active development and there is work being done on what is going to become 0.4.8 at some point, it has many changes (as listed below) but hasn’t yet been released.
But due to the wonders of technology, you can grab the unreleased development version from Github now (link also below).
WhatWeb CMS Identify Features
- Over 1700 plugins
- Control the trade-off between speed/stealth and reliability
- Performance tuning. Control how many websites to scan concurrently.
- Multiple log formats: Brief (greppable), Verbose (human readable), XML, JSON, MagicTree, RubyObject, MongoDB.
- Proxy support including TOR
- Custom HTTP headers
- Basic HTTP authentication
- Control over webpage redirection
- Nmap-style IP ranges
- Fuzzy matching
- Result certainty awareness
- Custom plugins defined on the command line
WhatWeb Sample Output
|
1 2 3 4 |
$ ./whatweb slashdot.org reddit.com http://reddit.com [302] HTTPServer[AkamaiGHost], RedirectLocation[http://www.reddit.com/], Via-Proxy[1.1 bc1], IP[173.223.232.64], Akamai-Global-Host, Country[UNITED STATES][US] http://slashdot.org [200] Script, HTTPServer[Unix][Apache/1.3.42 (Unix) mod_perl/1.31], Google-Analytics[GA][32013], Via-Proxy[1.1 bc5], UncommonHeaders[x-fry,x-varnish,x-xrds-location,slash_log_data], Apache[1.3.42][mod_perl/1.31], HTML5, IP[216.34.181.45], OpenGraphProtocol[100000696822412], X-Powered-By[Slash 2.005001], Title[Slashdot: News for nerds, stuff that matters], Email[[email protected],[email protected]], Country[UNITED STATES][US] http://www.reddit.com/ [200] Frame, PasswordField[passwd,passwd2], Script, HTTPServer['; DROP TABLE servertypes; --], IP[203.97.86.202], JQuery, Cookies[reddit_first], Title[reddit: the voice of the internet -- news before it happens], Country[NEW ZEALAND][NZ] |
Changes in 0.4.8-dev
- Added over 700 new plugins
- Added aggressive version detection using md5 static file matches to several plugins
- Added support for raw HTTP headers when scanning local files
- Added –dorks to return google dorks for the selected plugin
- Added google dorks to more than 500 plugins
- Added ./addons/hunter
- Added ./addons/gggooglescan
- Added ./addons/country-scanner
- Added SQL logging with
--log-sqland--log-sql-createarguments. - Added raw header support by monkey patching the net/http library
- Added context searching for plugin matches[].
- Added the matches keyword, :search.
- Added methods for aggressive plugins to send HEAD and POST requests
- Added –grep, -g option to be easier than –custom-plugin.
There are also other similar tools like:
– CMSmap – Content Management System Security Scanner
– Droopescan – Plugin Based CMS Security Scanner
– wig – CMS Identification & Information Gathering Tool
– BlindElephant – Web Application Fingerprinter
– Web-Sorrow v1.48 – Version Detection, CMS Identification & Enumeration
– Wappalyzer – Web Technology Identifier (Identify CMS, JavaScript etc.)
– WPScan – WordPress Security/Vulnerability Scanner
You can download the latest ‘stable’ dev version (if such a thing exists) here:
Or read more here.
