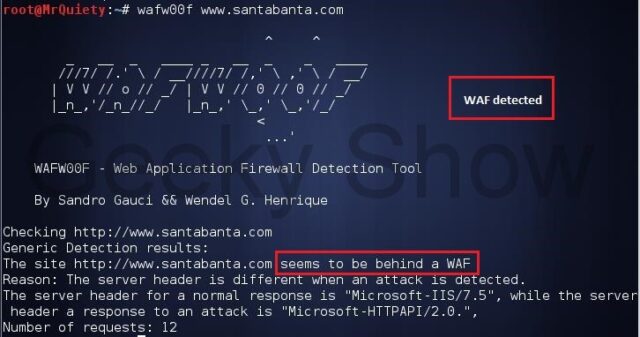
WAFW00F is a Python tool to help you fingerprint and identify Web Application Firewall (WAF) products. It is an active reconnaissance tool as it actually connects to the web server, but it starts out with a normal HTTP response and escalates as necessary.
You can override or include your own headers, it has SOCKS and HTTP proxy support and detects a whole bunch of WAF products from hosted solutions like CloudFlare and Incapsula to server side solutions like ModSecurity.
How does it work?
To do its magic, WAFW00F does the following:
- Sends a normal HTTP request and analyses the response; this identifies a number of WAF solutions
- If that is not successful, it sends a number of (potentially malicious) HTTP requests and uses simple logic to deduce which WAF it is
- If that is also not successful, it analyses the responses previously returned and uses another simple algorithm to guess if a WAF or security solution is actively responding to our attacks
What does it detect?
It detects a number of WAFs. To view which WAFs it is able to detect run WAFW00F with the -l option. At the time of writing the output is as follows:
- Anquanbao
- Juniper WebApp Secure
- IBM Web Application Security
- Cisco ACE XML Gateway
- F5 BIG-IP APM
- 360WangZhanBao
- ModSecurity (OWASP CRS)
- PowerCDN
- Safedog
- F5 FirePass
- DenyALL WAF
- Trustwave ModSecurity
- CloudFlare
- Imperva SecureSphere
- Incapsula WAF
- Citrix NetScaler
- F5 BIG-IP LTM
- Art of Defence HyperGuard
- Aqtronix WebKnight
- Teros WAF
- eEye Digital Security SecureIIS
- BinarySec
- IBM DataPower
- Microsoft ISA Server
- NetContinuum
- NSFocus
- ChinaCache-CDN
- West263CDN
- InfoGuard Airlock
- Barracuda Application Firewall
- F5 BIG-IP ASM
- Profense
- Mission Control Application Shield
- Microsoft URLScan
- Applicure dotDefender
- USP Secure Entry Server
- F5 Trafficshield
You can download here:
Or read more here.
