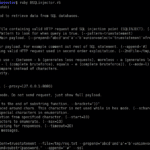
BSQLinjector is an easy to use Blind SQL Injection tool in Ruby, that uses blind methods to retrieve data from SQL databases. The download is below. The author recommends using the “–test” switch to clearly see how configured payload looks like before sending it to an application. What is Blind SQL Injection? Blind SQL Injection […]
Database Hacking
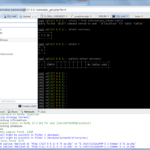
NoSQLMap – Automated NoSQL MongoDB Exploitation Tool
NoSQLMap is an open source Python-based automated NoSQL MongoDB exploitation tool designed to audit for as well as automate injection attacks and exploit default configuration weaknesses in NoSQL databases. It is also intended to attack web applications using NoSQL in order to disclose data from the database. What is NoSQLMap? Presently the tool’s exploits are […]
jSQL – Automatic SQL Injection Tool In Java
jSQL is an automatic SQL Injection tool written in Java, it’s lightweight and supports 23 kinds of database. It is free, open source and cross-platform (Windows, Linux, Mac OS X) and is easily available in Kali, Pentest Box, Parrot Security OS, ArchStrike or BlackArch Linux. Features of jSQL Java SQL Injection Tool Automatic injection of […]
mongoaudit – MongoDB Auditing & Pen-testing Tool
mongoaudit is a CLI tool for MongoDB auditing of servers, detecting poor security settings and performing automated penetration testing. It is widely known that there are quite a few holes in MongoDB’s default configuration settings. This fact, combined with abundant lazy system administrators and developers, has led to what the press has called the MongoDB […]
Another MongoDB Hack Leaks Two Million Recordings Of Kids
No surprises here, but there’s been another big MongoDB hack and from the looks of it, it’s been owned for quite some time. This time 2 million records from over 820,000 accounts have been leaked due to yet another default MongoDB installation with no authentication listening on the public IP address. The terrible part is, […]