Trape is an OSINT analysis tool, which allows people to track and execute intelligent social engineering attacks in real-time. It was created with the aim of teaching the world how large Internet companies could obtain confidential information. Example types of information are the status of sessions of their websites or services and control their users […]
Social Engineering
Fake News As A Service (FNaaS?) – $400k To Rig An Election
This is pretty interesting, the prices for Fake News as a Service have come out after some research by Trend Micro, imagine that you can create a fake celebrity with 300,000 followers for only $2,600. Now we all know this Fake News thing has been going on for a while, and of course, if it’s […]
SPF (SpeedPhish Framework) – E-mail Phishing Toolkit
SPF (SpeedPhish Framework) is a an e-mail phishing toolkit written in Python designed to allow for quick recon and deployment of simple social engineering phishing exercises. There are also other popular Phishing tools are frameworks such as: – Phishing Frenzy – E-mail Phishing Framework – Gophish – Open-Source Phishing Framework – sptoolkit Rebirth – Simple […]
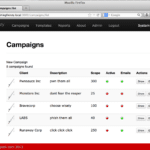
Phishing Frenzy – E-mail Phishing Framework
Phishing Frenzy is an Open Source Ruby on Rails e-mail phishing framework designed to help penetration testers manage multiple, complex phishing campaigns. The goal of the project is to streamline the phishing process while still providing clients the best realistic phishing campaign possible. This goal is obtainable through campaign management, template reuse, statistical generation, and […]
FSFlow – A Social Engineering Call Flow Application
FSFlow is a Social Engineering Call Flow Application, which was created to improve and standardize social engineering calls. It’s a difficult thing to do, conversations can go almost anywhere over the span of a phone call which makes defining a specific process hard, if not impossible. FSFlow is mostly a proof of concept tool but […]