Sandcastle is a Python-based Amazon AWS S3 Bucket Enumeration Tool, formerly known as bucketCrawler. The script takes a target’s name as the stem argument (e.g. shopify) and iterates through a file of bucket name permutations. Amazon S3 [Simple Storage Service] is cloud storage for the Internet. To upload your data (photos, videos, documents etc.), you […]
Hacking Tools
Hacking Tools are pieces of software or programs created to help you with hacking or that users can utilise for hacking purposes.
Examples include Wep0ff – Wifi Cracking Tool, Brutus Password Cracker, wwwhack Web Hacking, THC-Hydra Network Login Hacking and pwdump/fgdump Windows Password Dumping Tools.

You can find the latest and best hacking tools below and more on Wikipedia.
Script Kiddie Hacking Tools
There are various tools that are classified as too easy to use, or too automated and these fall into the category of Script Kiddie Tools. These are people who just follow instructions from a manual or tutorial without really understanding the technology or process happening.
Examples of these tools would mainly be password cracking tools like Cain and Abel Password Cracker, Brutus Password Cracker and John the Ripper for Password Cracking.
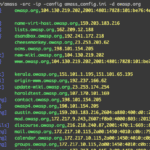
Judas DNS – Nameserver DNS Poisoning Attack Tool
Judas DNS is a Nameserver DNS Poisoning Attack Tool which functions as a DNS proxy server built to be deployed in place of a taken over nameserver to perform targeted exploitation. Judas works by proxying all DNS queries to the legitimate nameservers for a domain. The magic comes with Judas’s rule configurations which allow you […]
OWASP Amass – DNS Enumeration, Attack Surface Mapping & External Asset Discovery
The OWASP Amass Project is a DNS Enumeration, Attack Surface Mapping & External Asset Discovery tool to help information security professionals perform network mapping of attack surfaces and perform external asset discovery using open source information gathering and active reconnaissance techniques. Information Gathering Techniques Used by OWASP Amass for DNS Enumeration and More The main […]
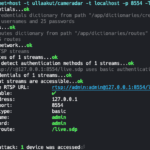
Cameradar – Hack RTSP Video Surveillance CCTV Cameras
Cameradar is a Go-based tool to hack RTSP Video Surveillance CCTV Cameras, it can detect open RTSP hosts, detect device models and launch automated attacks. The main features of Cameradar are: Detect open RTSP hosts on any accessible target host Detect which device model is streaming Launch automated dictionary attacks to get their stream route […]
dSploit APK Download – Hacking & Security Toolkit For Android
dSploit APK Download is a Hacking & Security Toolkit For Android which can conduct network analysis and penetration testing activities. It aims to offer to IT security experts the most complete and advanced professional toolkit to perform network security assessments on a mobile device. Once dSploit is started, you will be able to easily map […]