dSploit APK Download is a Hacking & Security Toolkit For Android which can conduct network analysis and penetration testing activities. It aims to offer to IT security experts the most complete and advanced professional toolkit to perform network security assessments on a mobile device.
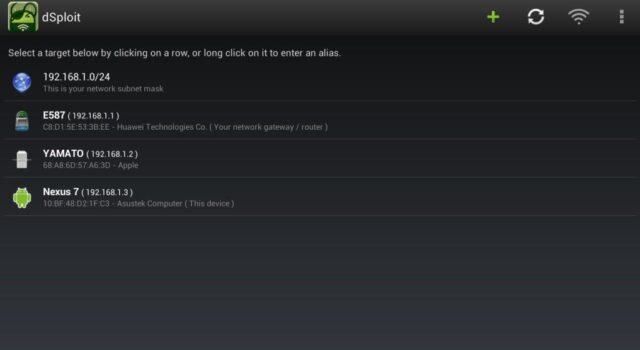
Once dSploit is started, you will be able to easily map your network, fingerprint alive hosts operating systems and running services, search for known vulnerabilities, crack logon procedures of many TCP protocols, perform man in the middle (MiTM) attacks such as password sniffing (with common protocols dissection), real-time traffic manipulation and more.
Features from dSploit APK Download Hacking Toolkit for Android
Features available on dSploit to hack using an Android phone:
- WiFi Cracking – The WiFi scanner will show in green access points with known default key generation algorithms, clicking on them allows you to easily crack the key
- RouterPWN – Launch the http://routerpwn.com/ service to pwn your router.
- Trace – Perform a traceroute on the target.
- Port Scanner – A syn port scanner to find quickly open ports on a single target.
- Inspector – Performs target operating system and services deep detection, slower than syn port scanner but more accurate.
- Vulnerability Finder – Search for known vulnerabilities for target running services upon the National Vulnerability Database.
- Login Cracker – A very fast network logon cracker which supports many different services.
- Packet Forger – Craft and send a custom TCP or UDP packet to the target, such as Wake On LAN packets.
- MITM – A set of Man-in-the-Middle (MitM) tools to command & conquer the whole network.
- Simple Sniff – Redirect target’s traffic through this device and show some stats while dumping it to a pcap file.
- Password Sniffer – Sniff passwords of many protocols such as HTTP, FTP, IMAP, IMAPS, IRC, MSN, etc from the target.
- Session Hijacker – Listen for cookies on the network and hijack sessions.
- Kill Connections – Kills connections preventing the target to reach any website or server.
- Redirect – Redirect all the HTTP traffic to another address.
- Replace Images – Replace all images on webpages with the specified one.
- Replace Videos – Replace all youtube videos on webpages with the specified one.
- Script Injection – Inject a javascript in every visited webpage.
- Custom Filter – Replace custom text on webpages with the specified one.
Requirements for dSploit APK Download To Work
For dSploit to work correctly you need:
– An ARM CPU
– Gingerbread Android (at least Android 2.3)
– Root
– A full install of BusyBox (every utility, not a partial install)
You can download dSploit here:
Source: dsploit-master.zip
APK: dsploit_1.0.31b.zip
Password for the APK .zip file is darknet123.
Or read more here.

Gonzalo says
It is a very useful tool, thanks for informing us of it
Adamu haladu says
Dsploit apk was not download why
And I’m a computer science students and I want join your team please
IV says
https://www.darknet.org.uk/content/files/dsploit_1.0.31b.zip
Shaheer says
Nice tool! The script injector is temperamental but does the job :)