New versions of the ultracool tools pwdump (1.4.2) and fgdump (1.3.4) have been released.
Both versions provide some feature upgrades as well as bug fixes. Folks with really old versions of either program should definitely look at upgrading since there are numerous performance improvements and full multithreading capabilities in both packages.
If you don’t know..what are pwdump6 and fgdump?
pwdump6 is a password hash dumper for Windows 2000 and later systems. It is capable of dumping LanMan and NTLM hashes as well as password hash histories. It is based on pwdump3e, and should be stable on XP SP2 and 2K3. If you have had LSASS crash on you using older tools, this should fix that.
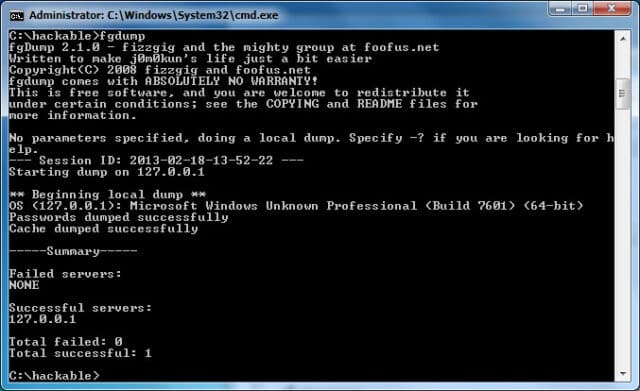
fgdump is a more powerful version of pwdump6. pwdump tends to hang and such when antivirus is present, so fgdump takes care of that by shutting down and later restarting a number of AV programs. It also can dump cached credentials and protected storage items and can be run in a multithreaded fashion very easily. I strongly recommend using fgdump, especially given that fgdump uses pwdump6 under the hood! You’ll get everything pwdump6 gives you and a lot more.
Darknet definitely DOES recommend fgdump, super cool update of the old favourite pwdump.
fgdump was born out of frustration with current antivirus (AV) vendors who only partially handled execution of programs like pwdump. Certain vendors’ solutions would sometimes allow pwdump to run, sometimes not, and sometimes lock up the box. As such, we as security engineers had to remember to shut off antivirus before running pwdump and similar utilities like cachedump. Needless to say, we’re forgetful sometimes…
So fgdump started as simply a wrapper around things we had to do to make pwdump work effectively. Later, cachedump was added to the mix, as were a couple other variations of AV. Over time it has grown, and continues to grow, to support our assessments and other projects. We are beginning to use it extensively within Windows domains for broad password auditing, and in conjunction with other tools (ownr and pwdumpToMatrix.pl) for discovering implied trust relationships.
What is fgdump for?
fgdump is targetted at the security auditing community, and is designed to be used for good, not evil. :) Note that, in order to effectively use fgdump, you’re going to need high-power credentials (Administrator or Domain Administrator, in most cases), thus limiting its usefulness as a hacking tool. However, hopefully some of you other security folks will find this helpful.
You can download pwdump here:
Or read more here.
And you can download fgdump here:
Or read more here.

qsin says
i lost my admin password for my pc standalone win xp..please i need help to recover my password or clear or reset…if there is a good software or advice on this i would really appreciate ..
Vlarol says
2qsin
See a nice tool at
http://home.eunet.no/pnordahl/ntpasswd/
r4v3n says
Cool, but when is there a 64-bit version available? I haven’t been able to extract any hashes from Windows 2003 x64 so far. Is that a safe system or am I just missing the right auditing tools?
Darknet says
r4v3n: I suggest you download the pwdump2 source code and compile it for 64 bit architecture (It’s not too hard to find). Good luck :)
Peter says
Does anyone understand these instructions on how to use it? I dont…. Could anyone please help me? I would love to try it try it out on my brothers pc… :p
I have pwdump 4 and 6. If anyone could help me out it would be great
thx in advance,
Peter
School Hacker says
Mwahahahahahahahaha!
zaman says
it true