evilscan is a Node.js based massive IP Port scanner designed for concurrency, speed and scanning large ranges of IP addresses. Features Individual IP or IP range scan Individual port, ports list, or port range Banner grabbing (not fully implemented, works with verbose ports only) IAC negotiation Reverse dns Geolocation information Shell or JSON output Optional progress […]
Networking Hacking Tools
Networking Hacking is an offensive branch of computer security related to networks hacking and the penetration of a target via the networking services or equipment.
Examples of network hacking tools include Kismet – Wireless Network Hacking, Sniffing & Monitoring, THC-Hydra – The Fast and Flexible Network Login Hacking Tool, Infernal Twin Updated 2.6.11 – Automated Wireless Hacking Suite and Firesheep – Social Network Session Stealing/Hijacking Tool.

Network hacking would also include WLAN hacking, wifi hacking, wireless hacking, Cisco hacking and so on which would rely on various different types of network hacking software.
Types of Networking Hacking
In this day and age, pretty much all hacking takes place across some kind of network (be it a private network or LAN, the public Internet, a darknet, public radio networks or any other kind).
You can find the best resources and networking hacking tools below.
Pybelt – The Hackers Tool Belt
Pybelt is a Python-based hackers tool belt capable of cracking hashes without prior knowledge of the algorithm, scanning ports on a given host, searching for SQLi vulnerabilities in a given URL, verifying that your Google dorks work like they should, verifying the algorithm of a given hash, scanning a URL for XSS vulnerability, and finding […]
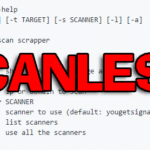
scanless – A Public Port Scan Scraper
scanless is a Python-based command-line utility that functions as a public port scan scraper, it can use websites that can perform port scans on your behalf. This is useful for early stages of penetration tests when you’d like to run a port scan on a host without having it originate from your IP address. Public […]
Ubertooth – Open Source Bluetooth Sniffer
Ubertooth is an open source Bluetooth sniffer and is essentially a development platform for Bluetooth experimentation. It runs best as a native Linux install and should work fine from within a VM. Ubertooth ships with a capable BLE (Bluetooth Smart) sniffer and can sniff some data from Basic Rate (BR) Bluetooth Classic connections. Features The […]
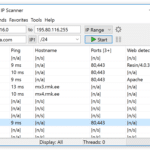
Angry IP Scanner Download – Fast Network IP Scanner
Angry IP scanner is a very easy to use, fast network IP scanner – basically a cross-platform IP address and port scanner. It can scan IP addresses in any range as well as any their ports, it’s also very lightweight and doesn’t require any installation, it can be freely copied and used anywhere. Angry IP […]