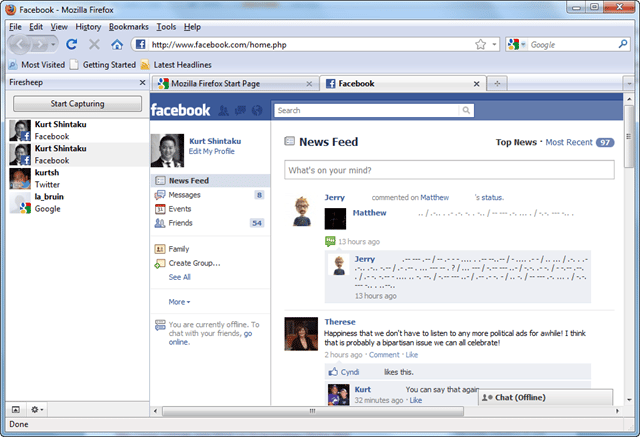
A huge wave has been made by this Firesheep in the mainstream media this week as it makes session hijacking a click and go procedure for Windows. It was released at Toorcon 12 and is simply a Firefox Add-on.
What is Firesheep?
Stealing sessions/passwords and so on is something we’ve been able to do for a LONG time using Wireshark or Ettercap on a hub based or WiFi network running without encryption. But now with Firesheep anyone can do it, and they can do it VERY easily, which is somewhat scary. It is incredibly easy to use, download the add-on, login to a public WiFi spot and click a button…you’ll then be shown images and usernames of various people using networks such as Facebook, Twitter, Flickr, bit.ly, Google and Amazon. With a double-click on their image, you’ll be logged in as them immediately.
Firesheep is free and open source and works on Mac OS X and Windows with Linux support being promised soon. The download rate of this add-on is epic with over 320,000 downloads in 3 days.
How to Protect Against Firesheep?
I expect you already know how to protect yourself from this kind of attack, but if you don’t…use a high-quality VPN like PureVPN whenever you are on a public Wifi spot! If you don’t have VPN access or can’t be arsed to set one up just make sure you force SSL/TLS on every site you surf – but do note to protect against this attack, you have to encrypt the entire session and not just the initial authentication.
Google has a secure search option too here – https://encrypted.google.com/
You can find the slides from the Toorcon 12 presentation here:
Hey Web 2.0: Start protecting user privacy instead of pretending to
Firesheep Session Hijacking Requirements
Windows users are required to install WinPcap.
Download Firesheep to Hack Facebook
You can download Firesheep v0.1 here:
Or read more here.

Bogwitch says
There is no new technology in use here, it is merely a tool to allow less technologically able users to see what the rest of us have been able to see for years.
It is raising an awareness of the need for ssl sessions for any restricted access web sites which can only be a good thing but there’s so much more than captured from unsecured network transmission mediums and users should be made aware of that, too.
As an aside, I would hate to be in the position of providing software like this – 100,000 users, 99% of whom will have NO idea if their NIC is capable of entering monitor/promisc mode and will automatically blame the software.
Darknet says
Yup, like I said at the beginning of the article – the only difference is this just makes it ridiculously easy. Heh honestly I don’t think the author gives a shit about supporting the users, it’s about proving a point more than anything else.
Hex says
I am still waiting on the Linux variant, hopefully out soon, so I can demonstrate this tool to people as awareness-raising. people dont ‘get’ wireshark dumps, but a mass-frape in the University would REALLY make the lesson STICK. Naturally, I would only target friends who are already pre-warned, and not frighten the life out of poor randoms.
Is there any easy way to ‘see’ if someone is using this on the network you are on?
Like a firesheep detector tool?
Darknet says
Yah if you pull all the packets off the network you should be able to figure it out, there’s no ‘tool’ for that though.
Graham says
Bogwitch,
The problem is the ease of access. Considering we are getting more mobile as a society, making it dumb simple to hack a wireless connection is not a good thing.
Tom Smith says
Combined with sslstrip it would be a scary tool. On the other hand… a HTTP notifier (addon or extension) on HTTPS sites would be a good idea.
Steve King says
For windows system, I have yet to find a laptop (running WinXP or Win7) that would support promiscuous mode on their wifi nic (Intel wifi nic). Is this true?
Darknet says
Most likely yah, pretty rare to find Windows machines (and off the shelf laptop WiFi cards) that can go promiscuous.
Steve King says
We know firesheep is not available for Linux machine (so far) and Windows machine rarely can do promiscuous mode, then what is the risk level?
BTW, does anyone know of development of firesheep-like feature under Linux?
Bogwitch says
For my pentesting laptop, I located a suitable card that would run promiscuous mode – but I also drilled a hole in the side of the laptop to fit a jack for a directional antenna and as you say, they are not standard cards.
As for running a similar software for Linux, perhaps tcpdump? ;P