Infernal Twin is an automated wireless hacking suite written in Python which automates many of the repetitive tasks involved in security testing for wifi networks.
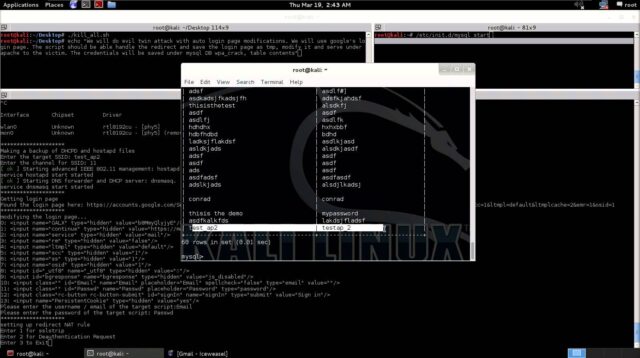
Originally created to automate the Evil Twin attack, it has grown much beyond that into a comprehensive suite including various wireless attack vectors.
An evil twin attack is when a hacker sets its service identifier (SSID) to be the same as an access point at the local hotspot or corporate wireless network. The hacker disrupts or disables the legitimate AP by disconnecting it, directing a denial of service against it, or creating RF interference around it.
Users lose their connections to the legitimate AP and re-connect to the “evil twin,” allowing the hacker to intercept all the traffic to that device.
Features
- WPA2 hacking
- WEP Hacking
- WPA2 Enterprise hacking
- Wireless Social Engineering
- SSL Strip
- Report Generation
- PDF Report
- HTML Report
- Note Taking
- Data saved in Database
- Network mapping
- MiTM
- Probe Request
Latest Changes
- Added Log retrieval button for various attack results.
- Added BeeF XSS framework Integration
- Added HTTP Traffic View within tool
- Improved Infenral Wireless Attack
- Visual View of some of the panel improved
- Improved Basic Authentication during Social engineering assessment over wireless network
You can download Infernal Twin here:
Or read more here.
