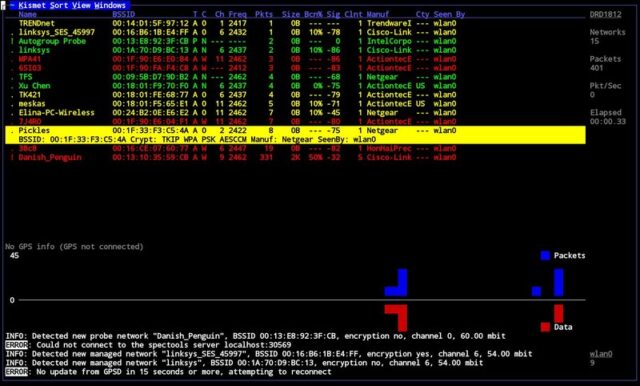
Kismet is an 802.11 layer2 wireless network detector, sniffer, and intrusion detection system. It will work with any wireless card which supports raw monitoring (rfmon) mode and can sniff 802.11b, 802.11a, and 802.11g traffic.
What is Kismet?
Kismet differs from other wireless network detectors in working passively. Namely, without sending any loggable packets, it is able to detect the presence of both wireless access points and wireless clients and to associate them with each other. It is also the most widely used and up to date open source wireless monitoring tool.
It also includes basic wireless IDS features such as detecting active wireless sniffing programs including NetStumbler, as well as a number of wireless network attacks and sports a plugin architecture allowing for additional non-802.11 protocols to be decoded.
Kismet Features
- 802.11 sniffing
- Standard PCAP logging (compatible with Wireshark, TCPDump, etc)
- Client/Server modular architecture
- Plug-in architecture to expand core features
- Multiple capture source support
- Live export of packets to other tools via tun/tap virtual interfaces
- Distributed remote sniffing via light-weight remote capture
- XML output for integration with other tools
In order to find as many networks as possible, it supports channel hopping. This means that it constantly changes from channel to channel non-sequentially, in a user-defined sequence with a default value that leaves big holes between channels (for example, 1-6-11-2-7-12-3-8-13-4-9-14-5-10). The advantage of this method is that it will capture more packets because adjacent channels overlap.
There are more Wireless Hacking tools here.
You can download Kismet latest version here:
Or read more here.

Goodpeople says
Personally I am an aircrack-ng kinda guy. But that is only if I want to break the encryption. Kismet is a very valueable tool for all other wireless related fun things you can think of.
Benjamin Juang says
And for those of us who are running MacOS X, there’s Kismac, the mac equivalent – I think we have almost everything Kismet has? (Was initially a port of Kismet to MacOS X, I think..? I may be wrong, don’t quote me on that.)
Am wondering though – has anyone tried it on windows? Or have a similar tool for windows?
Pantagruel says
As with most *nix apps you can use Cygwin to run then under Windows
(see http://www.kismetwireless.net/documentation.shtml)
You could give NetStumbler a try when tied to the Windows platform
DaCapn says
To the best of my knowledge there is only one card that works with kismet under windows. The windows drivers from the manufacturers do not support rfmon. Similarly, this means you can’t use the windows drivers with ndiswrapper on a unix-based system.
mumble says
@pantagruel – the problem is RFMON support. There is only one card with decent RFMON support for Win32, and that one is a specialty device for the wireless security market, and is expen$ive.
Right now, RFMON/packet injection tools are somewhat mature and capable for the free *nix operating systems, not bad for OSX, and pretty much worthless elsewhere. In fact, at this point – unless you like getting very intimate with the details of setting up kernel mode drivers, you’ll probably end up running something like Backtrack-3.
Arkwin says
http://www.oxid.it/
Cain & Able
http://www.netstumbler.com/
Net Stumbler
Emkayu says
If you’ve tried the OS X version of this, KisMac you will know how powerful and easy to use this is. Suppors reinjecting of packets, authentication floods, deauthenticating, and various cracking attacks (weak schedules, bruteforce and even wordlist attacks)
Yoshi says
First time reader! Don’t get me me wrong I think Kismet is a great tool, however i think a lot of the times you actually need to have some pretty pictures when presenting a wireless assessment / investigation / etc to mangement IMHO – more so with wireless than any other area for some reason (I guess it’s because you can’t see it so it makes it harder to grasp the concepts). Some times you got to pay the bucks to get the professional / graphical reporting
Nice blog! I’ll be back tomorrow to see the next post :)
eM3rC says
Commenting on Emkayu’s comment, 60 Minutes (CBS I think?) did a story about Kismet. More specifically, how it could be used to tap into stores wireless routes and steal credit card information. According to the story those little credit card scanners are wireless (the cords are power I guess) and when you swipe the card it gets sent to a modem which in turn is sent to the bank for conformation. Hackers were taping into these WEP protected modems (2-3 minutes to break if your really good, 10 for a normal user) and took the info passing through it.
I would say this is OSX’s aircrack-ng.
Pantagruel says
@Emkayu
True, I recently bought me a Mac Mini and it was quite a pain to find a supported wireless network dongle (got one through Ebay). Haven’t spend too much time playing with it.
Pantagruel says
Just for fun, go to kismac.de , it nicely sums up some of the postings here on DarkNet
Yoshi says
Oddly enough i’m actually in Germany this week. I may be way out of line here, but I think Germany has lost a lot of the organisation ‘lets do it the right way’ , hard work ethic it was once famous for – but then they have the workers council which is just a world of pain to deal with. (I don’t actually know the reason, but i would guess that the german work law is soo difficult that’s why Walmart never made a profit till the day they pulled out of Germany)
Obvisouly this is an outsiders view – German readers will have a far more informed opinion that little old me who visits on business every couple of months.
eM3rC says
Good point pantagruel. Thanks for the link!
DaCapn says
Was my previous post deleted for some reason? I don’t see it here now…
Netstumbler is a passive sniffer. Active sniffers like kismet are able to do things like discover APs that don’t broadcast their SSID.
eM3rC says
@DaCapn
Good point. Although to get into a modem that doesn’t broadcast its SSID seems like more questionable cracking ;)
eM3rC says
Got a kind of random post here.
For one of my classes I want to write a report on what exactly computer hacking is, what is happening with it today (groups, what they are doing, general modern hacker profile), and the history of it. As for material I have begun reading some books from the library (including Mitnick’s books).
If anyone could recommend any more material it would be much appreciated.
Pantagruel says
For some real old skool stuff try:
The cuckoo’s egg by Clifford Stoll
An Evening with Berferd by Bill Cheswick
More of this time:
Rootkits: Subverting the Windows Kernel (Addison-Wesley Software Security Series) by Greg Hoglund and Jamie Butler
Hacking: The Art of Exploitation, 2nd Edition by Jon Erickson
eM3rC says
Thanks a million Pantagruel!
The world needs to know hackers aren’t always bad ;)
If anyone else can recommend any material feel free to do so.
Emkayu says
theres a list of compatible dongles about, i personally use the Dlink DWL g122 on the RA-link build of kismac :D, can crack wep keys in local area under 10 minutes, link it with a GPS device and it’s great for wardriving with a macbook
Lee says
does anyone know if dell wireless 1390 wlan mini-card support the raw monitoring (rfmon) mode?? thanks.