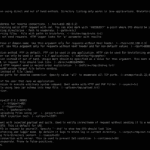
XXEinjector is a Ruby-based XXE Injection Tool that automates retrieving files using direct and out of band methods. Directory listing only works in Java applications and the brute forcing method needs to be used for other applications. Usage of XXEinjector XXE Injection Tool XXEinjector actually has a LOT of options, so do have a look […]
ruby
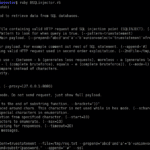
BSQLinjector – Blind SQL Injection Tool Download in Ruby
BSQLinjector is an easy to use Blind SQL Injection tool in Ruby, that uses blind methods to retrieve data from SQL databases. The download is below. The author recommends using the “–test” switch to clearly see how configured payload looks like before sending it to an application. What is Blind SQL Injection? Blind SQL Injection […]
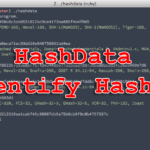
HashData – A Command-line Hash Identifying Tool
HashData is a Ruby-based command-line REPL Hash Identifying Tool with support for a lot of different (most popular) hash types. Installation
|
1 |
$ gem install hashdata |
Usage Command Line When installed, run hashdata and paste in hashes when prompted. Library Example Script:
|
1 2 3 |
require 'hashdata' hash = HashData.new puts(hash.check_type("1111111111111",'DES')) |
The above should output true. The library only matches the start of your second input, this […]
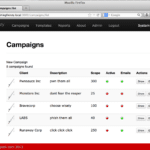
Phishing Frenzy – E-mail Phishing Framework
Phishing Frenzy is an Open Source Ruby on Rails e-mail phishing framework designed to help penetration testers manage multiple, complex phishing campaigns. The goal of the project is to streamline the phishing process while still providing clients the best realistic phishing campaign possible. This goal is obtainable through campaign management, template reuse, statistical generation, and […]
BetterCap – Modular, Portable MiTM Framework
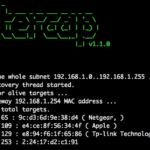
BetterCAP is a powerful, modular, portable MiTM framework that allows you to perform various types of Man-In-The-Middle attacks against the network. It can also help to manipulate HTTP and HTTPS traffic in real-time and much more. BetterCap has some pretty impressive Spoofing abilities with multiple host discovery (just launch the tool and it will start […]