Phishing Frenzy is an Open Source Ruby on Rails e-mail phishing framework designed to help penetration testers manage multiple, complex phishing campaigns. The goal of the project is to streamline the phishing process while still providing clients the best realistic phishing campaign possible. This goal is obtainable through campaign management, template reuse, statistical generation, and other features the Frenzy has to offer.
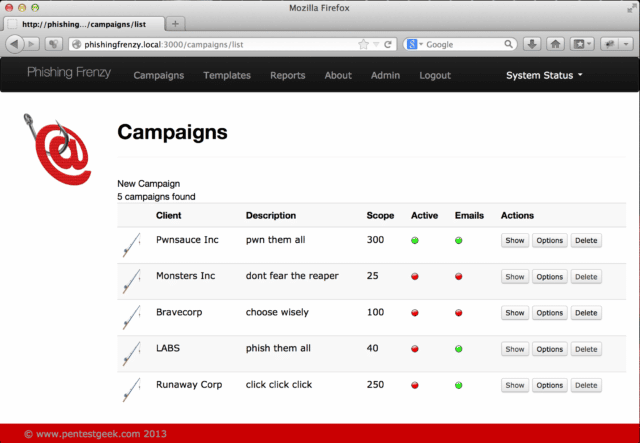
Leveraging the Twitter Bootstrap CSS library Phishing Frenzy is presented with an elegant front end that feels comfortable. Manage your phishing campaign with ease while looking good.
There are of course other frameworks and tools available too such as:
– Gophish – Open-Source Phishing Framework
– sptoolkit Rebirth – Simple Phishing Toolkit
– spt v0.6.0 – Simple Phishing Toolkit Available For Download
How It Works
Email Phishing in it’s simplest form consists of three (3) primary components.
- Sending Emails
- Hosting Websites
- Tracking Analytics
There obviously are more complex forms of email phishing that include additional components, but for the sake of our conversation we are going to break it up to this simple structure.
Features
- Website Cloning
- E-mail Harvesting
- Credential Harvesting
- UID tracking for users
- Reporting and Analytics
- Action Mailer
- Dynamic E-mails
- Preview E-mails
- Sharing Templates
- DataTables
- Export XML
- PDF Reports
You can download Phishing Frenzy by cloning the Github repo:
|
1 |
sudo git clone https://github.com/pentestgeek/phishing-frenzy.git /var/www/phishing-frenzy |
Or read more here.
