BetterCAP is a powerful, modular, portable MiTM framework that allows you to perform various types of Man-In-The-Middle attacks against the network. It can also help to manipulate HTTP and HTTPS traffic in real-time and much more.
BetterCap has some pretty impressive Spoofing abilities with multiple host discovery (just launch the tool and it will start discovery), ARP spoofing, DNS spoofing and ICMP doubledirect spoofing.
The other tool similar to this would be: MITMf – Man-In-The-Middle Attack Framework and specfically for SSL you have sslsniff v0.7 – SSL Man-In-The-Middle (MITM) Tool.
BetterCap MiTM Features
Some of the main features include:
- Full and half duplex ARP spoofing.
- The first real ICMP DoubleDirect spoofing implementation.
- Configurable DNS spoofing.
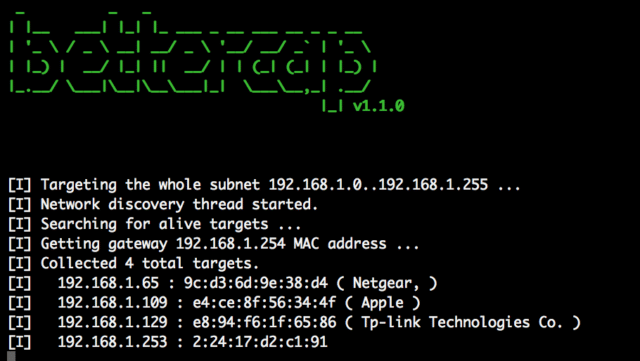
- Realtime and completely automatized host discovery.
- Realtime credentials harvesting for protocols such as HTTP(S) POSTed data, Basic and Digest Authentications, FTP, IRC, POP, IMAP, SMTP, NTLM ( HTTP, SMB, LDAP, etc ) and more.
- Fully customizable network sniffer.
- Modular HTTP and HTTPS transparent proxies with support for user plugins + builtin plugins to inject custom HTML code, JS or CSS files and URLs.
- SSLStripping with HSTS bypass.
- Builtin HTTP server.
Why BetterCap not Ettercap?
Ettercap still has some plus points like you can see connections and raw pcap stuff, but it’s not all relevant to everyone. Mostly it’s showing its’ age and BetterCap doesn’t have the below cons:
- Ettercap was a great tool, but it’s old
- Ettercap filters do not work most of the times
- Ettercap filters are outdated
- Ettercap filters are hard to implement due to the implementation language.
- Ettercap is unstable on big networks (try host discovery on a network bigger than /24)
- Ettercap is hard to extend or add modules to unless you’re a C/C++ developer.
- Ettercap’s and MITMf’s ICMP spoofing is completely useless in 2016.
- Ettercap does not provide a builtin and modular HTTP(S) transparent proxy.
- Ettercap does not provide a smart and fully customizable credentials sniffer.
You can download BetterCap via the Ruby gem system so:
|
1 |
sudo apt-get install build-essential ruby-dev libpcap-dev |
Then:
|
1 2 |
gem install bettercap gem update bettercap |
Kali Linux also has bettercap packaged, install it and all dependencies on the latest version of Kali using this:
|
1 2 |
apt-get update apt-get install bettercap |
Or read more here.

skriptkidd0r says
>Ettercap is hard to extend or add modules to unless you’re a C/C++ developer.
ahahaha fucking script kiddies are afraid of learning a real language
Bluecoder says
I think its not just people are script kiddies its just that some of us are know python or ruby or java and well this is a good framework for cutting that time in adding modules by learning C++