RWMC is a Windows PowerShell script written as a proof of concept to Retrieve Windows Credentials using only PowerShell and CDB command-line options (Windows Debuggers). It allows to retrieve credentials from Windows 2003 to 2012 and Windows 10 (It was tested on 2003, 2008r2, 2012, 2012r2 and Windows 7 – 32 and 64 bits, Windows […]
Archives for 2016
123456 Still The Most Common Password For 2015
So sadly, but also unsurprisingly ‘123456’ is still the most common password for 2015 (based on leaked password lists) the same as it was in years before, e.g. The 25 Worst Passwords Of 2013 – “password” Is Not #1. Way back in 2006, it clocked in at number 5 in a rather UK centric look […]
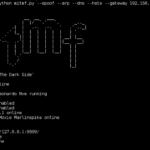
MITMf – Man-In-The-Middle Attack Tool
MITMf is a Man-In-The-Middle Attack Tool which aims to provide a one-stop-shop for Man-In-The-Middle (MiTM) and network attacks while updating and improving existing attacks and techniques. Originally built to address the significant shortcomings of other tools (e.g Ettercap, Mallory), it’s been almost completely re-written from scratch to provide a modular and easily extendible framework that […]
LOKI – Indicators Of Compromise Scanner
Loki is a Indicators Of Compromise Scanner, based on 4 main methods (additional checks are available) and will present a report showing GREEN, YELLOW or RED result lines. The compiled scanner may be detected by antivirus engines. This is caused by the fact that the scanner is a compiled python script that implement some file […]
Fortinet SSH Backdoor Found In Firewalls
So the Fortinet SSH Backdoor, apparently it’s just a management authentication issue. Sorry, what’s that? It looks like a passphrase based admin level access login via SSH to me personally. Which is scary. They are adamantly shouting from rooftops that it was not planted by a 3rd party (NSA? Like Juniper..) or any kind of […]