PowerShell Empire is a post-exploitation hacking tool built on cryptographically secure communications and a flexible architecture. Empire implements the ability to run PowerShell agents without needing powershell.exe, rapidly deployable post-exploitation modules ranging from key loggers to Mimikatz, and adaptable communications to evade network detection, all wrapped up in a usability-focused framework. It has a LOT […]
Archives for April 2016
BeautifulPeople.com Leak Exposes 1.1M Extremely Private Records
So another data breach, and no surprise here, but another dating site. This time the BeautifulPeople.com Leak has exposed 1.1 million customer records, including 15 million private messages sent between users. Not so private now is it. And no surprise either the entry point for this leak, was the not-so excellent NoSQL database MongoDB which […]
Google Rapid Response (GRR ) – Remote Live Forensics For Incident Response
GRR Rapid Response is an incident response framework focused on remote live forensics. It based on client server architecture, so there’s an agent which is installed on target systems and a Python server infrastructure that can manage and communicate with the agents. There are agents for Windows, Linux and Mac OS X environments. Overview To […]
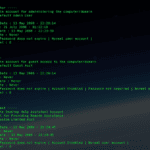
SamParser – Parse SAM Registry Hives With Python
SamParser is a Python script used to parse SAM registry hives for both users and groups, it’s only dependency is python-registry. This would be a great little script to write into another toolset or larger attack pattern, especially if you’re already using a Python kit or framework. Dependencies
|
1 |
pip install python-registry |
Usage
|
1 |
python samparse.py <hive> |
Sample Output
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 |
----- Administrator ----- Comment : Built-in account for administering the computer/domain Account Type : Default Admin User RID : 500 Account Created Date : 13 May 2008 - 22:20:14 Last Login Date : 21 July 2008 - 01:22:18 Password Reset Date : 13 May 2008 - 22:23:39 Password Fail Date : Never Account Flags : Password does not expire | Normal user account | Failed Login Count : 0 Login Count : 24 ----- Guest ----- Comment : Built-in account for guest access to the computer/domain Account Type : Default Guest Acct RID : 501 Account Created Date : 13 May 2008 - 22:20:14 Last Login Date : Never Password Reset Date : Never Password Fail Date : Never Account Flags : Password does not expire | Account Disabled | Password not required | Normal user account | Failed Login Count : 0 Login Count : 0 ----- Administrators ----- Group Description : Administrators have complete and unrestricted access to the computer/domain Last Write : 2008-05-14 05:35:35.281248 User Count : 7 Memebers : S-1-5-21-484763869-796845957-839522115-500 S-1-5-21-484763869-796845957-839522115-1003 S-1-5-21-484763869-796845957-839522115-1004 S-1-5-21-484763869-796845957-839522115-1005 S-1-5-21-484763869-796845957-839522115-1006 S-1-5-21-484763869-796845957-839522115-1007 S-1-5-21-484763869-796845957-839522115-1008 ----- Users ----- Group Description : Users are prevented from making accidental or intentional system-wide changes. Thus, Users can run certified applications, but not most legacy applications Last Write : 2008-05-14 05:35:35.265625 User Count : 8 Memebers : S-1-5-4 S-1-5-11 S-1-5-21-484763869-796845957-839522115-1003 S-1-5-21-484763869-796845957-839522115-1004 S-1-5-21-484763869-796845957-839522115-1005 S-1-5-21-484763869-796845957-839522115-1006 S-1-5-21-484763869-796845957-839522115-1007 S-1-5-21-484763869-796845957-839522115-1008 |
You […]
Apple Will Not Patch Windows QuickTime Vulnerabilities
Much like Adobe Flash, QuickTime from Apple is a bit of a relic some pretty serious, remote code execution type Windows QuickTime Vulnerabilities were recently discovered by Trend Micro. Apple has officially stated that they won’t be fixing them and the official line on this, is to uninstall QuickTime. I guess a lot of people […]