SamParser is a Python script used to parse SAM registry hives for both users and groups, it’s only dependency is python-registry.
This would be a great little script to write into another toolset or larger attack pattern, especially if you’re already using a Python kit or framework.
Dependencies
|
1 |
pip install python-registry |
Usage
|
1 |
python samparse.py <hive> |
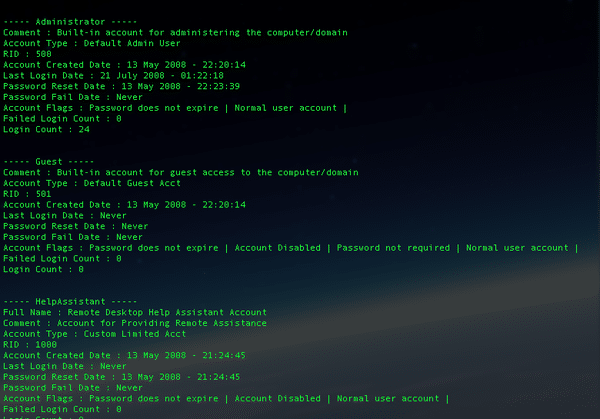
Sample Output
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 |
----- Administrator ----- Comment : Built-in account for administering the computer/domain Account Type : Default Admin User RID : 500 Account Created Date : 13 May 2008 - 22:20:14 Last Login Date : 21 July 2008 - 01:22:18 Password Reset Date : 13 May 2008 - 22:23:39 Password Fail Date : Never Account Flags : Password does not expire | Normal user account | Failed Login Count : 0 Login Count : 24 ----- Guest ----- Comment : Built-in account for guest access to the computer/domain Account Type : Default Guest Acct RID : 501 Account Created Date : 13 May 2008 - 22:20:14 Last Login Date : Never Password Reset Date : Never Password Fail Date : Never Account Flags : Password does not expire | Account Disabled | Password not required | Normal user account | Failed Login Count : 0 Login Count : 0 ----- Administrators ----- Group Description : Administrators have complete and unrestricted access to the computer/domain Last Write : 2008-05-14 05:35:35.281248 User Count : 7 Memebers : S-1-5-21-484763869-796845957-839522115-500 S-1-5-21-484763869-796845957-839522115-1003 S-1-5-21-484763869-796845957-839522115-1004 S-1-5-21-484763869-796845957-839522115-1005 S-1-5-21-484763869-796845957-839522115-1006 S-1-5-21-484763869-796845957-839522115-1007 S-1-5-21-484763869-796845957-839522115-1008 ----- Users ----- Group Description : Users are prevented from making accidental or intentional system-wide changes. Thus, Users can run certified applications, but not most legacy applications Last Write : 2008-05-14 05:35:35.265625 User Count : 8 Memebers : S-1-5-4 S-1-5-11 S-1-5-21-484763869-796845957-839522115-1003 S-1-5-21-484763869-796845957-839522115-1004 S-1-5-21-484763869-796845957-839522115-1005 S-1-5-21-484763869-796845957-839522115-1006 S-1-5-21-484763869-796845957-839522115-1007 S-1-5-21-484763869-796845957-839522115-1008 |
You can download SamParser here:
Or read more here.
