GRR Rapid Response is an incident response framework focused on remote live forensics. It based on client server architecture, so there’s an agent which is installed on target systems and a Python server infrastructure that can manage and communicate with the agents.
There are agents for Windows, Linux and Mac OS X environments.
Overview
To function, an agent is deployed on systems that one might want to investigate. Once deployed, each system becomes a GRR client and they can start receiving messages from the frontend servers. Each message tells the client to run a specific client action and return the results. A client action is simply some well known code the agent knows how to execute (such as obtaining the list of files in a directory or reading a buffer from a file).
These actions are invoked server-side through what we call flows. A flow is a piece of server-side code that asks the GRR system to schedule remote calls to a client and has some additional logic to decide what to do based on the call results.
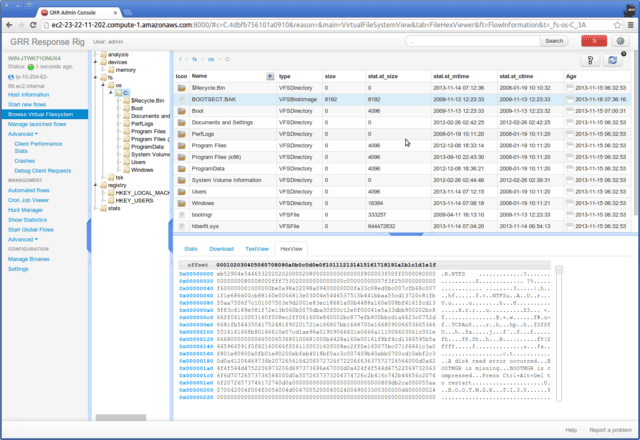
This flow is running on a client because a user initiated it. To do so, he probably used the web-based Graphical User Interface (GUI), which allows a GRR user to start flows for clients and review the results. Or he could also have used the text-based console to do the same.
Any flow that can be run on a single machine can also be run as a Hunt. A hunt allows running a flow on all, or any subset of machines talking to the GRR server.
Client Features
- Cross-platform support for Linux, OS X and Windows clients.
- Live remote memory analysis using open source memory drivers for Linux, OS X and Windows via the Rekall memory analysis framework.
- Powerful search and download capabilities for files and the Windows registry.
- Secure communication infrastructure designed for Internet deployment.
- Client automatic update support.
- Detailed monitoring of client CPU, memory, IO usage and self-imposed limits.
Server Features
- Fully fledged response capabilities handling most incident response and forensics tasks.
- OS-level and raw file system access, using the SleuthKit (TSK).
- Enterprise hunting (searching across a fleet of machines) support.
- Fully scalable back-end to handle very large deployments.
- Automated scheduling for recurring tasks.
- Fast and simple collection of hundreds of digital forensic artifacts.
- Asynchronous design allows future task scheduling for clients, designed to work with a large fleet of laptops.
- AngularJS Web UI and RESTful JSON API.
- Fully scriptable IPython console access.
- Basic system timelining features.
- Basic reporting infrastructure.
You can download GRR here:
1. Run the Docker image, info here: https://github.com/google/grr-doc/blob/master/docker.adoc
2. Install fresh on a Linux system, needs 1GB RAM (AWS free instance isn’t powerful enough):
|
1 2 |
wget https://raw.githubusercontent.com/google/grr/master/scripts/install_script_ubuntu.sh sudo bash install_script_ubuntu.sh |
Or read more here.
