PowerShell Empire is a post-exploitation hacking tool built on cryptographically secure communications and a flexible architecture. Empire implements the ability to run PowerShell agents without needing powershell.exe, rapidly deployable post-exploitation modules ranging from key loggers to Mimikatz, and adaptable communications to evade network detection, all wrapped up in a usability-focused framework.
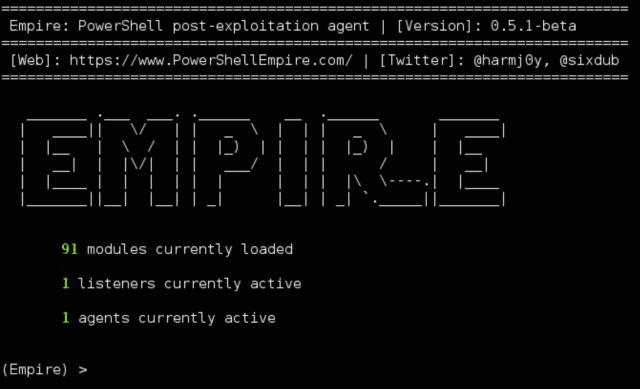
It has a LOT of modules (90+) and is currently in the midst of implementing a RESTful API which will be great.
PowerShell Empire Module Categories
Currently Empire Power Shell has the following categories for modules:
- Code Execution – Ways to run more code
- Collection – Post exploitation data collection
- Credentials – Collect and use creds
- Exfiltration – Identify egress channels
- Lateral Movement – Move around the network
- Management – Host management and auxilary
- Persistence – Survive reboots
- Privesc – Privilege escalation capabilities
- Recon – Test further entry points (HTTP Basic Auth etc)
- Situational Awareness – Network awareness
- Trollsploit – For the lulz
Why Empire PowerShell?
PowerShell offers a multitude of offensive advantages, including:
- Full .NET access
- Application whitelisting
- Direct access to the Win32 API
- Ability to assemble malicious binaries in memor
- Default installation on Windows 7+.
Powershell for Pentesters had a watershed year in 2014, but despite the multitude of useful projects, many pen-testers still struggle to integrate PowerShell into their engagements in a secure manner.
How PowerShell Empire Hacking Tools Works
Empire has a few components which you can chain together, similar to something like Metasploits.
It has:
Listeners – Think of this like a metasploit handler, this will catch your session.
Stagers – This is your payload, this is what you will execute on your target system.
Agents – This is how you interact with the target system, you can gather stats & info or run shell commands.
It also had fairly robust logging built in.
You can download PowerShell Empire here:
Or read more here.
