wig is a web application information gathering tool, which can identify numerous Content Management Systems and other administrative applications. It’s strength is CMS identification, it can also attempt to do OS fingerprinting.
The application fingerprinting is based on checksums and string matching of known files for different versions of CMSes. This results in a score being calculated for each detected CMS and its versions. Each detected CMS is displayed along with the most probable version(s) of it. The score calculation is based on weights and the amount of “hits” for a given checksum.
wig also tries to guess the operating system on the server based on the ‘server’ and ‘x-powered-by’ headers. A database containing known header values for different operating systems is included in wig, which allows wig to guess Microsoft Windows versions and Linux distribution and version.
Version 0.5 has just been tagged/released on Github and there are a bunch of changes since our previous posting in 2014 – wig – WebApp Information Gatherer – Identify CMS
There are various other tools which perform similar functions such as CMS identification and issue detection:
– CMSmap – Content Management System Security Scanner
– Droopescan – Plugin Based CMS Security Scanner
– WhatWeb – Identify CMS, Blogging Platform, Stats Packages & More
– BlindElephant – Web Application Fingerprinter
– Web-Sorrow v1.48 – Version Detection, CMS Identification & Enumeration
– Wappalyzer – Web Technology Identifier (Identify CMS, JavaScript etc.)
– WPScan – WordPress Security/Vulnerability Scanner
Features
- CMS version detection by: check sums, string matching and extraction
- Lists detected package and platform versions such as asp.net, php, openssl, apache
- Detects JavaScript libraries
- Operation system fingerprinting by matching php, apache and other packages against a values in wig’s database
- Checks for files of interest such as administrative login pages, readmes, etc
- Currently the wig’s databases include 28,000 fingerprints
- Reuse information from previous runs (save the cache)
- Implement a verbose option
- Remove dependency on ‘requests’
- Support for proxy
- Proper threading support
- Included check for known vulnerabilities
Changes Since wig v.01
- Added fingerprints for more CMS, OS, platforms
- Improved and updated old fingerprints
- Proxy support
- List vulnerabilies associated with detected software version
- Added detection of JavaScript libs
- General site information (currently title, cookie, ip)
- Removed requirement for 3rd party python libs (requests). Now only requires Python3
- Improved verbose output
- Added a cache
- Improved structure of the output
- Detection of generally interesting files (readme, backups, etc)
- Implemented proper threading via thread pool
Requirements
wig is built with Python 3, and is therefore not compatible with Python 2.
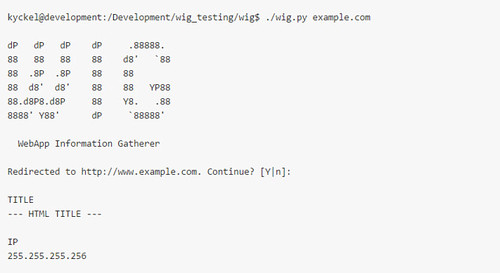
Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 |
usage: wig.py [-h] [-n STOP_AFTER] [-a] [-m] [-u] [--no_cache_load] [--no_cache_save] [-N] [--verbosity] [--proxy PROXY] url WebApp Information Gatherer positional arguments: url The url to scan e.g. http://example.com optional arguments: -h, --help show this help message and exit -n STOP_AFTER Stop after this amount of CMSs have been detected. Default: 1 -a Do not stop after the first CMS is detected -m Try harder to find a match without making more requests -u User-agent to use in the requests --no_cache_load Do not load cached responses --no_cache_save Do not save the cache for later use -N Shortcut for --no_cache_load and --no_cache_save --verbosity, -v Increase verbosity. Use multiple times for more info --proxy PROXY Tunnel through a proxy (format: localhost:8080) |
You can download wig v0.5 here:
Or read more here.
