WAFNinja is a Python-based Web Application Firewall Attack Tool designed to help penetration testers execute WAF bypass by automating the steps necessary to bypass input validation. The tool was created with the objective to be easily extendible, simple to use and usable in a team environment. What can WAFNinja Web Application Firewall Attack Tool Do? […]
waf
Microsoft Azure Web Application Firewall (WAF) Launched
Not too long after Amazon launched their cloud protection WAF the Microsoft Azure Web Application Firewall (WAF) has been made generally available in all public Azure DCs. It’s a good move with the majority of websites and services moving into one of the big 3 cloud providers (AWS, Google or Azure) and the vast majority […]
Raptor WAF – C Based Web Application Firewall
Raptor WAF is a Web Application Firewall made in C, using DFA to block SQL Injection, Cross Site Scripting (XSS) and Path Traversal. DFA stands for Deterministic Finite Automaton also known as a Deterministic Finite State Machine. It’s essentially a simple web application firewall made in C, using the KISS principle, making polls using the […]
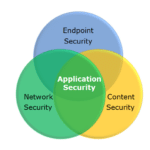
An Introduction To Web Application Security Systems
In the world of web application security systems, there exists a myriad of systems to protect public-facing services in any number of ways. They come packed with all the elements necessary to play an action-packed round of buzzword bingo, but they often overlap in some ways that may make them sometimes seem similar. After the second […]
WAFW00F – Fingerprint & Identify Web Application Firewall (WAF) Products
WAFW00F is a Python tool to help you fingerprint and identify Web Application Firewall (WAF) products. It is an active reconnaissance tool as it actually connects to the web server, but it starts out with a normal HTTP response and escalates as necessary. You can override or include your own headers, it has SOCKS and […]