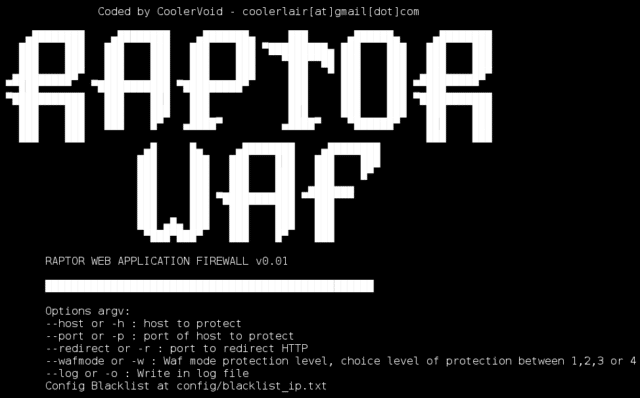
Raptor WAF is a Web Application Firewall made in C, using DFA to block SQL Injection, Cross Site Scripting (XSS) and Path Traversal.
DFA stands for Deterministic Finite Automaton also known as a Deterministic Finite State Machine.
It’s essentially a simple web application firewall made in C, using the KISS principle, making polls using the select() function, it’s not better than epoll() or kqueue() from *BSD but it is portable.
Features
WAF stands for Web Application Firewall. It is widely used nowadays to detect and defend against most commonly SQL Injections and XSS attacks.
- Block XSS, SQL Injection attacks and path traversal
- Blacklist IPs to block users using config/blacklist ip.txt
- Supports IPv6 and IPv4 for communication
Coming in the Future
- DoS protection
- Request limits
- Rule interpreter
- Malware detection for uploads
- SSL/TLS Support
Do bear in mind this is an early stage almost PoC tool and not really production tested or ready, I think it’d be a great project to contribute to and most people don’t need a super complex WAF – just something REALLY reliable, stable, performant and blocks 80-90% of the common attacks.
Other options for a WAF:
– NAXSI – Open-Source WAF For Nginx
– Amazon AWS Web Application Firewall (WAF ) Launched
– ModSecurity – Open Source Web Application Firewall
You can download Raptor WAF here:
Or read more here.
