Domained is a multi tool subdomain enumeration tool that uses several subdomain enumeration tools and wordlists to create a unique list of subdomains that are passed to EyeWitness for reporting.
This produces categorized screenshots, server response headers and signature based default credential checking. It is written in Python heavily leveraging Recon-ng.
Domains Subdomain Enumeration Tools Leveraged
Subdomain Enumeraton Tools:
Reporting + Wordlists:
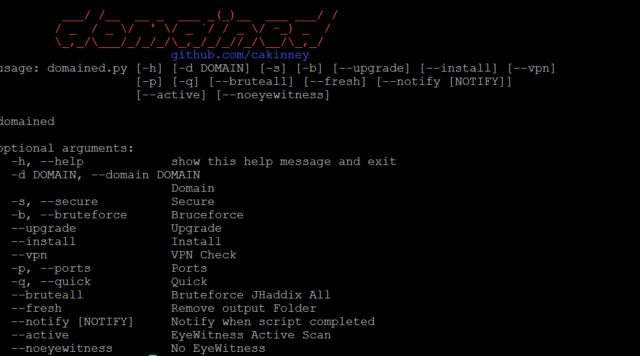
Domained Subdomain Enumeration Tool Usage
|
1 2 3 4 5 6 7 8 9 10 11 12 |
--install/--upgrade Both do the same function – install all prerequisite tools --vpn Check if you are on VPN (update with your provider) --quick Use ONLY Amass and SubFinder --bruteall Bruteforce with JHaddix All.txt List instead of SecList --fresh Delete old data from output folder --notify Send Pushover or Gmail Notifications --active EyeWitness Active Scan --noeyewitness No Eyewitness -d The domain you want to preform recon on -b Bruteforce with subbrute/massdns and SecList wordlist -s n Only HTTPs domains -p Add port 8080 for HTTP and 8443 for HTTPS |
Subdomain Enumeration Examples
First Steps are to install required Python modules and tools:
|
1 2 |
sudo pip install -r ./ext/requirements.txt sudo python domained.py --install |
Example 1 – Uses subdomain example.com (Sublist3r (+subbrute), enumall, Knock, Amass, and SubFinder)
|
1 |
python domained.py -d example.com |
Example 2: – Uses subdomain example.com with seclist subdomain list bruteforcing (massdns, subbrute, Sublist3r, Amass, enumall, and SubFinder), adds ports 8443/8080 and checks if on VPN
|
1 |
python domained.py -d example.com -b -p --vpn |
Example 3: – Uses subdomain example.com with large-all.txt bruteforcing (massdns, subbrute, Sublist3r, Amass, enumall and SubFinder)
|
1 |
python domained.py -d example.com -b --bruteall |
Example 4: – Uses subdomain example.com and only Amass and SubFinder
|
1 |
python domained.py -d example.com --quick |
Example 5: – Uses subdomain example.com, only Amass and SubFinder and notification
|
1 |
python domained.py -d example.com --quick --notify |
Example 6: – Uses subdomain example.com with no EyeWitness
|
1 |
python domained.py -d example.com --noeyewitness |
Note: --bruteall must be used with the -b flag
You can download Domained here:
Or read more here.
