Recon-ng is a full-featured Web Reconnaissance Framework written in Python. Complete with independent modules, database interaction, interactive help, and command completion – Recon-ng provides a powerful environment in which open source web-based reconnaissance can be conducted quickly and thoroughly.
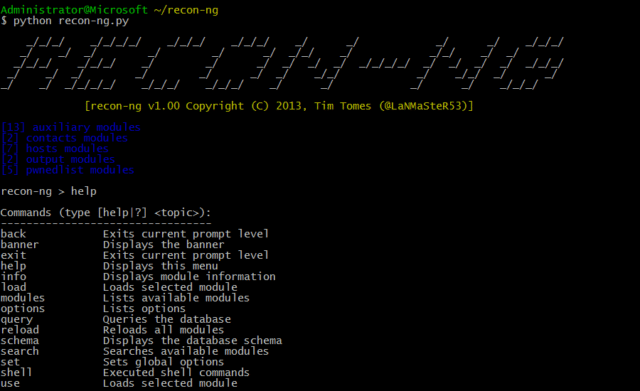
Recon-ng has a look and feel and even command flow similar to the Metasploit Framework, reducing the learning curve for leveraging the framework. It is of course quite different though, Recon-ng is not designed to compete with existing frameworks, as it is designed exclusively for web-based open source reconnaissance.
If you want to exploit, use the Metasploit Framework. If you want to social engineer, use the Social-Engineer Toolkit. If you want to conduct passive reconnaissance, use Recon-ng!
An example on active reconnaissance would be Skipfish by the Google Security Team.
What is Recon-ng?
Recon ng is a completely modular framework and makes it easy for even the newest of Python developers to contribute. Each module is a subclass of the “module” class. The “module” class is a customized “cmd” interpreter equipped with built-in functionality that provides simple interfaces to common tasks such as standardizing output, interacting with the database, making web requests, and managing API keys. Therefore, all the hard work has been done. Building modules is simple and takes little more than a few minutes.
Recon-ng Modules
Recon-ng comes with ~80 recon moduloes, 2 discovery modules, 2 exploitation modules, 7 reporting modules and 2 import modules.
- cache_snoop – DNS Cache Snooper
- interesting_files – Interesting File Finder
- command_injector – Remote Command Injection Shell Interface
- xpath_bruter – Xpath Injection Brute Forcer
- csv_file – Advanced CSV File Importer
- list – List File Importer
- point_usage – Jigsaw – Point Usage Statistics Fetcher
- purchase_contact – Jigsaw – Single Contact Retriever
- search_contacts – Jigsaw Contact Enumerator
- jigsaw_auth – Jigsaw Authenticated Contact Enumerator
- linkedin_auth – LinkedIn Authenticated Contact Enumerator
- github_miner – Github Resource Miner
- whois_miner – Whois Data Miner
- bing_linkedin – Bing Linkedin Profile Harvester
- email_validator – SalesMaple Email Validator
- mailtester – MailTester Email Validator
- mangle – Contact Name Mangler
- unmangle – Contact Name Unmangler
- hibp_breach – Have I been pwned? Breach Search
- hibp_paste – Have I been pwned? Paste Search
- pwnedlist – PwnedList Validator
- migrate_contacts – Contacts to Domains Data Migrator
- facebook_directory – Facebook Directory Crawler
- fullcontact – FullContact Contact Enumerator
- adobe – Adobe Hash Cracker
- bozocrack – PyBozoCrack Hash Lookup
- hashes_org – Hashes.org Hash Lookup
- leakdb – leakdb Hash Lookup
- metacrawler – Meta Data Extractor
- pgp_search – PGP Key Owner Lookup
- salesmaple – SalesMaple Contact Harvester
- whois_pocs – Whois POC Harvester
- account_creds – PwnedList – Account Credentials Fetcher
- api_usage – PwnedList – API Usage Statistics Fetcher
- domain_creds – PwnedList – Pwned Domain Credentials Fetcher
- domain_ispwned – PwnedList – Pwned Domain Statistics Fetcher
- leak_lookup – PwnedList – Leak Details Fetcher
- leaks_dump – PwnedList – Leak Details Fetcher
- brute_suffix – DNS Public Suffix Brute Forcer
- baidu_site – Baidu Hostname Enumerator
- bing_domain_api – Bing API Hostname Enumerator
- bing_domain_web – Bing Hostname Enumerator
- brute_hosts – DNS Hostname Brute Forcer
- builtwith – BuiltWith Enumerator
- google_site_api – Google CSE Hostname Enumerator
- google_site_web – Google Hostname Enumerator
- netcraft – Netcraft Hostname Enumerator
- shodan_hostname – Shodan Hostname Enumerator
- ssl_san – SSL SAN Lookup
- vpnhunter – VPNHunter Lookup
- yahoo_domain – Yahoo Hostname Enumerator
- zone_transfer – DNS Zone File Harvester
- ghdb – Google Hacking Database
- punkspider – PunkSPIDER Vulnerabilty Finder
- xssed – XSSed Domain Lookup
- xssposed – XSSposed Domain Lookup
- migrate_hosts – Hosts to Domains Data Migrator
- bing_ip – Bing API IP Neighbor Enumerator
- freegeoip – FreeGeoIP
- ip_neighbor – My-IP-Neighbors.com Lookup
- ipinfodb – IPInfoDB GeoIP
- resolve – Hostname Resolver
- reverse_resolve – Reverse Resolver
- ssltools – SSLTools.com Host Name Lookups
- geocode – Address Geocoder
- reverse_geocode – Reverse Geocoder
- flickr – Flickr Geolocation Search
- instagram – Instagram Geolocation Search
- picasa – Picasa Geolocation Search
- shodan – Shodan Geolocation Search
- twitter – Twitter Geolocation Search
- whois_orgs – Whois Company Harvester
- reverse_resolve – Reverse Resolver
- shodan_net – Shodan Network Enumerator
- census_2012 – Internet Census 2012 Lookup
- sonar_cio – Project Sonar Lookup
- migrate_ports – Ports to Hosts Data Migrator
- dev_diver – Dev Diver Repository Activity Examiner
- linkedin – Linkedin Contact Crawler
- linkedin_crawl – Linkedin Profile Crawler
- namechk – NameChk.com Username Validator
- profiler – OSINT HUMINT Profile Collector
- twitter – Twitter Handles
- github_repos – Github Code Enumerator
- gists_search – Github Gist Searcher
- github_dorks – Github Dork Analyzer
- csv – CSV File Creator
- html – HTML Report Generator
- json – JSON Report Generator
- list – List Creator
- pushpin – PushPin Report Generator
- xlsx – XLSX File Creator
- xml – XML Report Generator
Recon ng Dependencies
All 3rd party libraries/packages should be installed prior to use. The framework checks for the presence of the following dependencies at runtime and disables the modules affected by missing dependencies.
- dnspython
- dicttoxml
- jsonrpclib
- lxml
- mechanize
- slowaes
- XlsxWriter
You can download Recon-ng here:
|
1 |
To install:
Change into the Recon-ng directory.
|
1 |
cd recon-ng |
Install dependencies.
|
1 |
pip install -r REQUIREMENTS |
Or read on how to use Recon-ng here.
