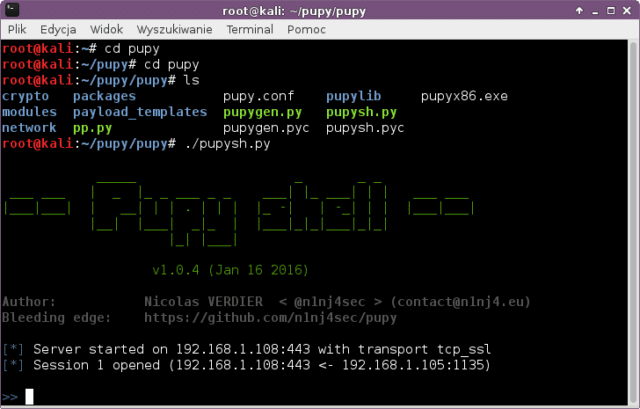
Pupy is an open-source remote administration tool (RAT), that is cross-platform and has an embedded Python interpreter, allowing its modules to load Python packages from memory and transparently access remote Python objects. Pupy can communicate using different transports and have a bunch of cool features & modules. On Windows, Pupy uses reflective dll injection and leaves no traces on disk.
This is absolutely killer for the Python crowd and gives the possibility of a pure Python worm, with in-memory ONLY execution of Python modules on the target. That means no detection by malware scanners as it doesn’t touch the disk like the meterpreter reverse_shell.
Pupy RAT Features
Pupy has a fairly complete feature set and covers the following:
- Multi-platform (tested on windows xp, 7, 8, 10, kali linux, ubuntu, osx, android)
- On windows, the Pupy payload can be compiled as a reflective DLL and the whole python interpreter is loaded from memory. Pupy does not touch the disk :)
- pupy can also be packed into a single .py file and run without any dependencies other that the python standard library on all OS
- pycrypto gets replaced by pure python aes && rsa implementations when unavailable
- Can reflectively migrate into other processes
- Can remotely import, from memory, pure python packages (.py, .pyc) and compiled python C extensions (.pyd, .so). The imported python modules do not touch the disk.
- Easily extensible, modules are quite simple to write, sorted by os and category.
- A lot of awesome modules are already implemented!
- Pupy uses rpyc and a module can directly access python objects on the remote client
- We can also access remote objects interactively from the pupy shell and you even get auto-completion of remote attributes!
- Communication transports are modular, stackable and awesome. You could exfiltrate data using HTTP over HTTP over AES over XOR. Or any combination of the available transports !
- Cn communicate using obfsproxy pluggable transports
- All the non interactive modules can be dispatched to multiple hosts in one command
- Commands and scripts running on remote hosts are interruptible
- Auto-completion for commands and arguments
- Custom config can be defined: command aliases, modules automatically run at connection, …
- Interactive python shells with auto-completion on the all in memory remote python interpreter can be opened
- Interactive shells (cmd.exe, /bin/bash, …) can be opened remotely. Remote shells on Unix & windows clients have a real tty with all keyboard signals working fine just like a ssh shell
- Execute PE exe remotely and from memory (cf. ex with mimikatz)
- Generate payloads in various formats : apk,lin_x86,lin_x64,so_x86,so_x64,exe_x86,exe_x64,dll_x86,dll_x64,py,pyinst,py_oneliner,ps1,ps1_oneliner,rubber_ducky
- Can be deployed in memory, from a single command line using pupygen.py’s python or powershell one-liners.
- “scriptlets” can be embeded in generated payloads to perform some tasks “offline” without needing network connectivity (ex: start keylogger, add persistence, execute custom python script, check_vm …)
The imported python modules do not touch the disk. (.pyd mem import currently work on Windows only, .so memory import is not implemented). And rpyc can also access remote objects interactively from the pupy shell and even auto completion of remote attributes works.
Pupy Open Source RAT Modules
-
All platforms:
- command execution
- download
- upload
- interactive python shell with auto-completion
- interactive shell (cmd.exe, powershell.exe, /bin/sh, /bin/bash, …)
- tty allocation is well supported on both windows and *nix. Just looks like a ssh shell
- shellcode exec
- persistence
- socks5 proxy
- local and remote port forwarding
- screenshot
- keylogger
- run the awesome credential gathering tool LaZagne from memory !
- sniff tools, netcreds
- process migration (windows & linux, not osx yet)
- …
- a lot of other tools (upnp client, various recon/pivot tools using impacket remotely, …)
Windows specific :
- migrate
- inter process architecture injection also works (x86->x64 and x64->x86)
- in memory execution of PE exe both x86 and x64!
- works very well with mimitakz :-)
- webcam snapshot
- microphone recorder
- mouselogger:
- takes small screenshots around the mouse at each click and send them back to the server
- token manipulation
- getsystem
- creddump
- tons of useful powershell scripts
- …
Android specific
- Text to speech for Android to say stuff out loud
- webcam snapshots (front cam & back cam)
- GPS tracker !
You can download Pupy here:
Or read more here.
