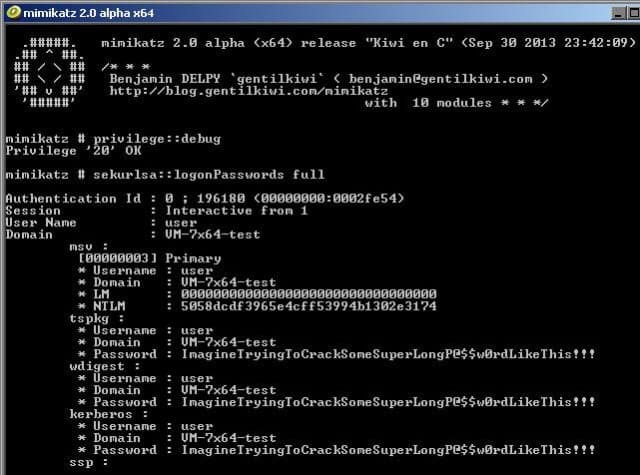
Mimikatz is a tool to gather Windows credentials, basically a swiss-army knife of Windows credential gathering that bundles together many of the most useful tasks that you would perform on a Windows machine you have SYSTEM privileges on. It supports both Windows 32-bit and 64-bit and allows you to gather various credential types.
What is Mimikatz?
Many people refer to it as a post-exploitation tool, something you would use to take a stronger hold of a network already compromised.
It carries out techniques such as Pass the Hash, Pass the Ticket, Over-Pass The Hash (AKA Pass the Key), Kerberos Golden Ticket, Kerberos Silver Ticket, Pass the Cache & Attacking the Kerberos Session Ticket (TGS).
Mimikatz Features
- Dump credentials from LSASS (Windows Local Security Account database)
- MSV1.0: hashes & keys (dpapi)
- Kerberos password, ekeys, tickets, & PIN
- TsPkg (password)
- WDigest (clear-text password)
- LiveSSP (clear-text password)
- SSP (clear-text password)
- Generate Kerberos Golden Tickets (Kerberos TGT logon token ticket attack)
- Generate Kerberos Silver Tickets (Kerberos TGS service ticket attack)
- Export certificates and keys (even those not normally exportable).
- Dump cached credentials
- Stop event monitoring.
- Bypass Microsoft AppLocker / Software Restriction Polcies
- Patch Terminal Server
- Basic GPO bypass
Commands
The primary command components are sekurlsa, kerberos, crypto, vault, and lsadump.
Sekurlsa interacts with the LSASS process in memory to gather credential data and provides enhanced capability over kerberos.
The Mimikatz kerberos command set enables modification of Kerberos tickets and interacts with the official Microsoft Kerberos API. This is the command that creates Golden Tickets. Pass the ticket is also possible with this command since it can inject Kerberos ticket(s) (TGT or TGS) into the current session. External Kerberos tools may be used for session injection, but they must follow the Kerberos credential format (KRB_CRED). Mimikatz kerberos also enables the creation of Silver Tickets which are Kerberos tickets (TGT or TGS) with arbitrary data enabling AD user/ group
Crypto enables export of certificates on the system that are not marked exportable since it bypasses the standard export process.
Vault enables dumping data from the Windows vault.
Lsadump enables dumping credential data from the Security Account Manager (SAM) database which contains the NTLM (sometimes LM hash) and supports online and offline mode as well as dumping credential data from the LSASS process in memory. Lsadump can also be used to dump cached credentials. In a Windows domain, credentials are cached (up to 10) in case a Domain Controller is unavailable for authentication. However, these credentials are stored on the computer.
Mimikatz Windows OS Support
Mimikatz works on:
- Windows XP
- Windows Vista
- Windows 7
- Windows 8
- Windows Server 2003
- Windows Server 2008 / 2008 R2
- Windows Server 2012 / 2012 R2
- Windows 10 (beta support)
You can download mimikatz most recent release here:
Or read more here.
