[ad] SQL Power Injector is a graphical application created in .NET 1.1 that helps the penetrating tester to inject SQL commands on a web page. For now it is SQL Server, Oracle and MySQL compliant, but it is possible to use it with any existing DBMS when using the inline injection (Normal mode). Moreover this […]
sql-hacking
sqlget v1.0.0 – Blind SQL Injection Tool in PERL
sqlget is a blind SQL injection tool developed in Perl, it lets you get databases schemas and tables rows. Using a single GET/POST you can access quietly the database structure and using a single GET/POST you can dump every table row to a csv-like file. Databases supported: IBM DB2 Microsoft SQL Server Oracle Postgres Mysql […]
SQLBrute – SQL Injection Brute Force Tool
[ad] SQLBrute is a tool for brute forcing data out of databases using blind SQL injection vulnerabilities. It supports time based and error based exploit types on Microsoft SQL Server, and error based exploit on Oracle. It is written in Python, uses multi-threading, and doesn’t require non-standard libraries (there is some code in there for […]
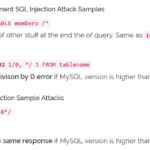
Comprehensive SQL Injection Cheat Sheet
A reader e-mailed me a while ago about a fairly comprehensive SQL Injection Cheat Sheet they had created and posted up. I compared it to the other ones I had bookmarked, and it was different enough to be worth posting. Currently only for MySQL and Microsoft SQL Server, some ORACLE and some PostgreSQL. Most of […]
sqlmap – Automated Blind SQL Injection Tool
[ad] sqlmap is an automatic blind SQL injection tool, developed in python, capable of enumerating an entire remote database, performing an active database fingerprint and much more. The aim of this project is to implement a fully functional database mapper tool which takes advantages of web application programming security flaws which lead to SQL injection […]