A reader e-mailed me a while ago about a fairly comprehensive SQL Injection Cheat Sheet they had created and posted up.
I compared it to the other ones I had bookmarked, and it was different enough to be worth posting.
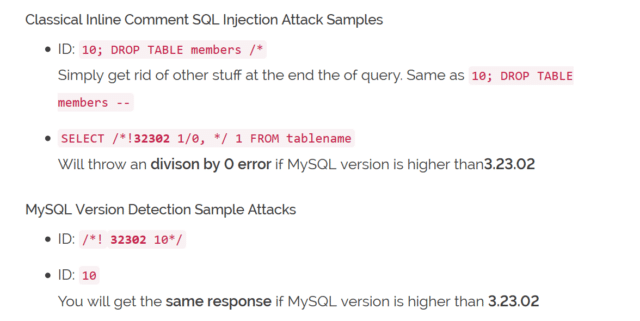
Currently only for MySQL and Microsoft SQL Server, some ORACLE and some PostgreSQL. Most of samples are not correct for every single situation. Most of the real world environments may change because of parenthesis, different code bases and unexpected, strange SQL sentences.
Samples are provided to allow reader to get basic idea of a potential attack and almost every section includes a brief information about itself.
SQL Injection Cheat Sheet
It’s worthy resource to save on your hacking pen-drive and bookmark in your portable Firefox.
https://www.netsparker.com/blog/web-security/sql-injection-cheat-sheet/

backbone says
it’s a great cheat sheet, but it very heavely based on sql and ms sql servers… the most killer stuff (chapter 12) has only 2-3 sub chapters where there are discused also mysql injection codes… but if you need sql and ms sql injection codes, this is the best that I have seen… it’s also the first when you search on google “sql injection cheat sheet” :)
Torvaun says
Excellent, one more resource that I didn’t already have in quality. Darknet strikes again!
Daniel says
I actually learned how to do manual SQL injections from this thing and the links provided. like 3 months ago maybe.
Its sweet.
I just copied and pasted code, then started to understand it.
J. Lion says
Good Resource (bookmarked)
Pantagruel says
Indeed a very nice cheat sheet. Am not really into databse pentesting, but we will have a shake down of an in-house generated db soon. Guess I’ll have to check this cheat sheet and do some trying.
eM3rC says
Bookmarked and on my list of things to study.
@Pantagruel
If you decided to become a black hat I bet all hell would break loose ;P