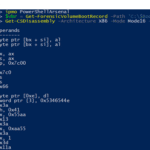
PowerShellArsenal is basically PowerShell for reverse engineering in a module format. The module can be used to disassemble managed and unmanaged code, perform .NET malware analysis, analyse/scrape memory, parse file formats and memory structures, obtain internal system information, etc. PowerShellArsenal is comprised of the following tools: Disassembly – Disassemble native and managed code. MalwareAnalysis – […]
reverse-engineering
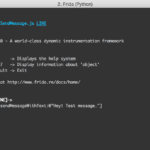
Frida – Dynamic Code Instrumentation Toolkit
Frida is basically Greasemonkey for native apps, or, put in more technical terms, it’s a dynamic code instrumentation toolkit. It lets you inject snippets of JavaScript into native apps on Windows, Mac, Linux, iOS and Android. Frida also provides you with some simple tools built on top of the Frida API. These can be used […]
Malwarebytes Bug Bounty Program Goes Live
So Malwarebytes bug bounty program is live, the official name is actually Malwarebytes Coordinated Vulnerability Disclosure Program – what a mouthful (guidelines here). It’s good to see, bug bounty programs typically tend to have a nett positive effect and end in win-win situations for researchers and software vendors alike. In an effort to encourage researchers […]
Radare – The Reverse Engineering Framework
Radare started out as a simple command line interface for a hexadecimal editor supporting 64 bit offsets to make searches and recovering data from hard-disks. It has evolved into a project that is composed of a hexadecimal editor as the central point of the project with assembler/disassembler, code analysis, scripting features, analysis and graphs of […]
Capstone – Multi-platform, Multi-architecture Disassembly Framework
Capstone is a lightweight multi-platform, multi-architecture disassembly framework. The target of the author is to make Capstone the ultimate disassembly engine for binary analysis and reversing in the security community. It is one of a very few disassembly frameworks that can support multi-architectures. So far, it can handle 4 most important architectures: ARM, ARM64 (aka […]