Radare started out as a simple command line interface for a hexadecimal editor supporting 64 bit offsets to make searches and recovering data from hard-disks. It has evolved into a project that is composed of a hexadecimal editor as the central point of the project with assembler/disassembler, code analysis, scripting features, analysis and graphs of code and data and easy unix integration. Essentially, it has become a reverse engineering framework, with plugins and much more.
radare2 itself is the core of the hexadecimal editor and debugger. Allows to open any kind of file from different IO access like disk, network, kernel plugins, remote devices, debugged processes and handle any of them as if they were a simple plain file.
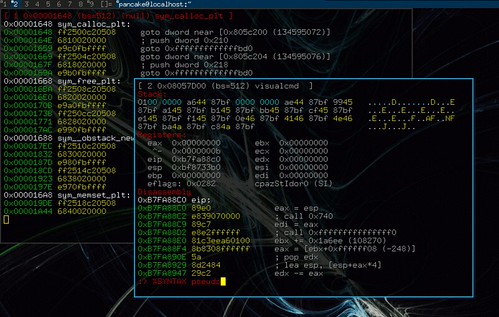
It implements an advanced command line interface for moving around the file, analyzing data, disassembling, binary patching, data comparision, searching, replacing, scripting with Ruby, Python, Lua and Perl.
Features
- CLI and visual modes
- Yank and paste
- Perl/Python scripting support
- Virtual base address for on-disk patching
- vi-like environment and command repetition (3x)
- Debugger for x86-linux/bsd and arm-linux
- Data bookmarking (flags)
- Scripting (no branches or conditionals yet)
- Own magic database (rfile)
- Little/big endian conversions
- Data search
- Show xrefs on arm, x86 and ppc binaries
- Data type views
- Data block views
- Visual mode commands
You can download radare here:
Or read more here – the author can be found on Twitter here @trufae.
