mongoaudit is a CLI tool for MongoDB auditing of servers, detecting poor security settings and performing automated penetration testing.
It is widely known that there are quite a few holes in MongoDB’s default configuration settings. This fact, combined with abundant lazy system administrators and developers, has led to what the press has called the MongoDB Ransack.
And just last week we wrote about Another MongoDB Hack Leaks Two Million Recordings Of Kids.
mongoaudit not only detects misconfigurations, known vulnerabilities and bugs but also gives you advice on how to fix them, recommends best practices and teaches you how to DevOp like a pro!
Features
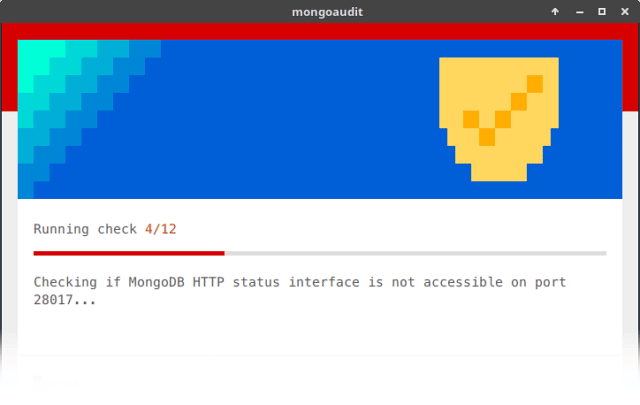
mongoaudit tests that:
- MongoDB listens on a port different to default one
- Server only accepts connections from whitelisted hosts / networks
- MongoDB HTTP status interface is not accessible on port 28017
- MongoDB is not exposing its version number
- MongoDB version is newer than 2.4
- TLS/SSL encryption is enabled
- Authentication is enabled
- SCRAM-SHA-1 authentication method is enabled
- Server-side Javascript is forbidden
- Roles granted to the user only permit CRUD operations
- The user has permissions over a single database
Once you run any of the test suites provided by mongoaudit, it will offer you to receive a fully detailed report via email. This personalised report links to a series of useful guides on how to fix every specific issue and how to harden your MongoDB deployments.
You can download mongoaudit here:
Or read more here.
