PingCastle is a Active Directory Security Assessment Tool designed to quickly assess the Active Directory security level with a methodology based on a risk assessment and maturity framework. It does not aim at a perfect evaluation but rather as an efficiency compromise.
The risk level regarding Active Directory security has changed. Several vulnerabilities have been made popular with tools like mimikatz or sites likes adsecurity.org.
CMMI is a well known methodology from the Carnegie Mellon university to evaluate the maturity with a grade from 1 to 5, PingCastle has adapated CMMI to Active Directory security.
The aim of the tool is to get you to 80% AD security in 20% of the time it would traditionally take.
PingCastle Active Directory Security Assessment Tool Features
Health Check
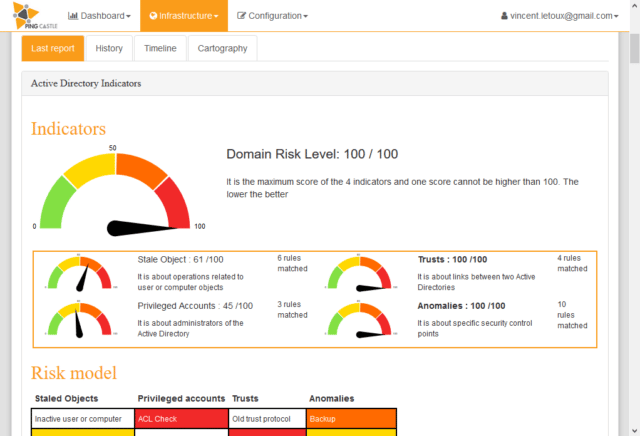
This is the default report produced by PingCastle. It quickly collects the most important information of the Active Directory and establish an overview. Based on a model and rules, it evaluates the score of the sub-processes of the Active Directory. Then it reports the risks.
Active Directory map
This report produce a map of all Active Directory that PingCastle knows about. This map is built based on existing health check reports or when none is available, via a special mode collecting the required information as fast as possible.
Deploy and collect reports
Monitoring domains from a bastion can be easy. But for those without network connection it might be difficult. There are many deployment strategies available with PingCastle.
Consolidation
When multiple reports of PingCastle have been collected, they can be regrouped in a single report. This facilitates the benchmark of all domains.
Scanner
Checking workstations for local admin privileges, open shares, startup time is usually complex and requires an admin. PingCastle’s scanner bypass these classic limits.
Using Pingcastle Active Directory Security Assessment Tool
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 |
|:. PingCastle (Version 2.5.2.0) | #:. Get Active Directory Security at 80% in 20% of the time # @@ > End of support: 31/07/2020 | @@@: .: https://www.pingcastle.com Using interactive mode. Do not forget that there are other command line switches like --help that you can use What you would like to do? 1-healthcheck-Score the risk of a domain 2-graph -Analyze admin groups and delegations 3-conso -Aggregate multiple reports into a single one 4-nullsession-Perform a specific security check 5-carto -Build a map of all interconnected domains 6-scanner -Perform specific security checks on workstations |
You can download Pingcastle here:
Or read more here.

bob says
for anyone wondering, this is not a remote tool, it must be installed locally