coWPAtty is a C-based tool for running a brute-force dictionary attack against WPA-PSK and audit pre-shared WPA keys.
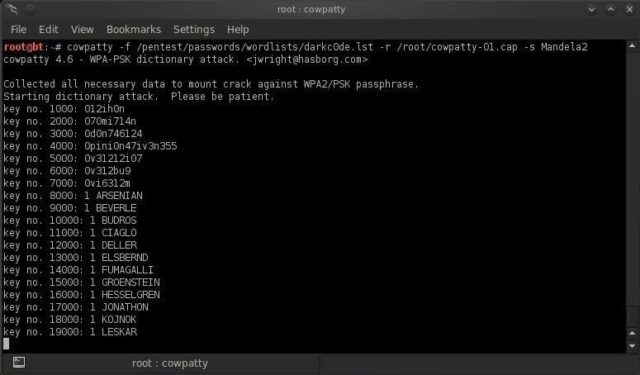
If you are auditing WPA-PSK networks, you can use this tool to identify weak passphrases that were used to generate the PMK. Supply a libpcap capture file that includes the 4-way handshake, a dictionary file of passphrases to guess with, and the SSID for the network.
What is coWPAtty?
coWPAtty is the implementation of an offline dictionary attack against WPA/WPA2 networks using PSK-based authentication (e.g. WPA-Personal). Many enterprise networks deploy PSK-based authentication mechanisms for WPA/WPA2 since it is much easier than establishing the necessary RADIUS, supplicant and certificate authority architecture needed for WPA-Enterprise authentication. coWPAtty can implement an accelerated attack if a precomputed PMK file is available for the SSID that is being assessed.
coWPAtty Usage
Example:
|
1 |
./cowpatty -r eap-test.dump -f dict -s somethingclever |
Full Output:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
cowpatty -h cowpatty 4.6 - WPA-PSK dictionary attack. <jwright@hasborg.com> Usage: cowpatty [options] -f Dictionary file -d Hash file (genpmk) -r Packet capture file -s Network SSID (enclose in quotes if SSID includes spaces) -c Check for valid 4-way frames, does not crack -h Print this help information and exit -v Print verbose information (more -v for more verbosity) -V Print program version and exit |
This tool can also accept dictionary words from STDIN, allowing us to utilize a tool such as John the Ripper to create lots of word permutations from a dictionary file.
|
1 2 |
john -wordfile:dictfile -rules -session:johnrestore.dat -stdout:63 | \ cowpatty -r eap-test.dump -f - -s somethingclever |
In the default configuration of John the Ripper, common permutations of dictionary words will be sent as potential passwords to coWPAtty.
This tool is based around the whitepaper by Robert Moskowitz:
Weakness in Passphrase Choice in WPA Interface
There are also the following to check out:
– wifite – Mass Wifi WEP / WPA Key Cracking Tool
– aircrack-ng – WEP and WPA-PSK Key Cracking Program
– Reaver Download – Hack WPS Pin WiFi Networks
coWPAtty download
You can download coWPAtty here:
Or read more here.
