OpenPuff is a professional steganography tool, with unique features you won’t find among any other free or commercial software. OpenPuff is 100% free and suitable for highly sensitive data covert transmission.
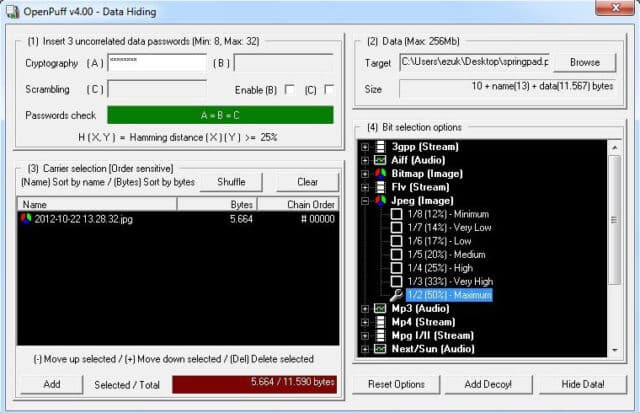
The tool contains deniable steganography, carrier chains, unique layers of security and obfuscation, multiple carrier formats, is portable and is freeware (ad-free).
Features of OpenPuff Steganography Tool
- Carrier chains – Data is split among many carriers. Only the correct carrier sequence enables unhiding. Moreover, up to 256Mb can be hidden, if you have enough carriers at disposal. Last carrier will be filled with random bits in order to make it undistinguishable from others.
- Supported formats – Images, audios, videos, flash, adobe.
- Layers of security – Data, before carrier injection, is encrypted (1), scrambled (2), whitened (3) and encoded (4).
- Extra security (Deniable steganography) – Top secret data can be protected using less secret data as a decoy.
- Source code – This program relies on the libObfuscate system-independent open-source library.
Details of OpenPuff Steganography Tool
- HW seeded random number generator (CSPRNG)
- Deniable steganography
- Carrier chains (up to 256Mb of hidden data)
- Carrier bits selection level
- Modern multi-cryptography (16 algorithms)
- Multi-layered data obfuscation (3 passwords)
- X-squared steganalysis resistance
- 256bit+256bit symmetric-key cryptography (with KDF4 password extension)
- 256bit symmetric-key data scrambling (CSPRNG-based shuffling)
- 256bit symmetric-key data whitening (CSPRNG-based noise mixing)
- Adaptive non-linear carrier bit encoding
- Images (BMP, JPG, PCX, PNG, TGA)
- Audio support (AIFF, MP3, NEXT/SUN, WAV)
- Video support (3GP, MP4, MPG, VOB)
- Flash-Adobe support (FLV, SWF, PDF)
- Native portable structure (no installation, registry keys, .ini files)
- Runs in user mode with DEP on
- Multithread support (up to 16 CPUs) = Faster processing
- Spyware/adware-free
- Fully redistributable
- OpenSource core crypto-library (libObfuscate)
You could also check out more Steganography related tools here:
– spectrology – Basic Audio Steganography Tool
– StegExpose – Steganalysis Tool For Detecting Steganography In Images
You can download OpenPuff here:
Or read more here.
