StegExpose is a steganalysis tool specialized in detecting steganography in lossless images such as PNG and BMP (LSB – least significant bit type). It has a command line interface and is designed to analyse images in bulk while providing reporting capabilities and customization which is comprehensible for non forensic experts.
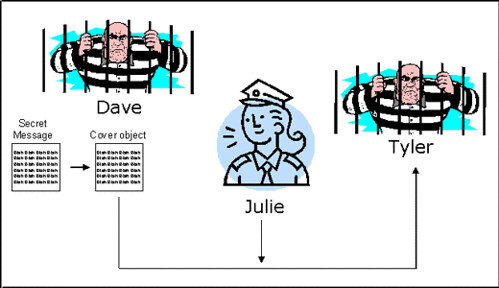
Steganography is the art or practice of concealing a message, image, or file within another message, image, or file. The word steganography combines the Ancient Greek words steganos, meaning “covered, concealed, or protected”, and graphein meaning “writing”.
StegExpose rating algorithm is derived from an intelligent and thoroughly tested combination of pre-existing pixel based staganalysis methods including:
- Sample Pairs by Dumitrescu (2003)
- RS Analysis by Fridrich (2001)
- Chi Square Attack by Westfeld (2000)
- Primary Sets by Dumitrescu (2002)
In addition to detecting the presence of steganography, StegExpose also features the quantitative steganalysis (determining the length of the hidden message).
Usage
|
1 |
java -jar StegExpose.jar [directory] [speed] [threshold] [csv file] |
[directory] – directory containing images to be diagnosed
[speed] – Optional. Can be set to ‘default’ or ‘fast’ (set to ‘default if left blank). default mode will try and run all detectors whereas fast mode will skip the expensive detectors in case cheap detectors are able to determine if a file is clean.
[threshold] – Optional. The default value here is 0.2 (for both speed modes) and determines the the level at which files are considered to be hiding data or not. A floating point value between 0 and 1 can be used here to update the threshold. If keeping false positives at bay is of priority, set the threshold slightly higher ~0.25. If reducing false negatives is more important, set the threshold slightly lower ~0.15
[csv file] – Optional. Name of the csv (comma separated value) file that is to be generated. that If left blank, the program will simply output to the console.
Performance
The accuracy and speed of StegExpose has been tested on an image pool of 15,200 lossless images, where 5,200 of them were stego images (images with hidden data) created with the tools OpenStego, OpenPuff, SilentEye and LSB-Steganography. Embedding rates range from 2.5% to 25.3% with an average of 13.8% (secret data / cover image).
You can download StegExpose here:
Or read more here.
