Winpayloads is a tool to provide undetectable Windows payload generation with some extras running on Python 2.7.
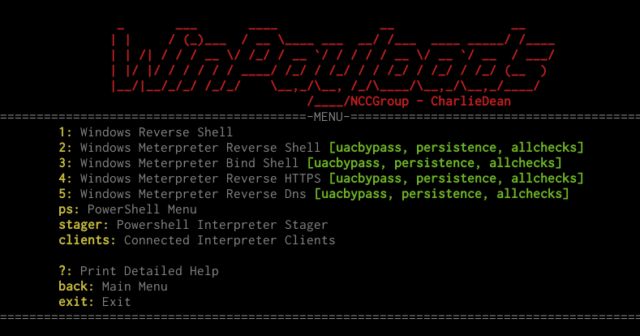
It provides persistence, privilege escalation, shellcode invocation and much more. The tool uses metasploits meterpreter shellcode, injects the users IP and port into the shellcode and writes a python file that executes the shellcode using ctypes. This is then AES encrypted and compiled to a Windows Executable using pyinstaller.
Features
- UACBypass – PowerShellEmpire
- PowerUp – PowerShellEmpire
- Invoke-Shellcode
- Invoke-Mimikatz
- Invoke-EventVwrBypass
- Persistence – Adds payload persistence on reboot
- Psexec Spray – Spray hashes until successful connection and psexec payload on target
- Upload to local webserver – Easy deployment
- Powershell stager – allows invoking payloads in memory & more
Winpayloads also comes with a few features such as UAC bypass and payload persistence. These are powershell files that execute on the system when the meterpreter gets a reverse shell. The UAC bypass is written by PowerShellEmpire and uses an exploit to bypass UAC on local administrator accounts and creates a reverse meterpreter running as local administrator back to the attackers machine.
Winpayloads can also setup a SimpleHTTPServer to put the payload on the network to allow downloading on the target machine and also has a psexec feature that will execute the payload on the target machine if supplied with usernames,domain,passwords or hashes.
Installation
git clone https://github.com/nccgroup/winpayloads.gitcd winpayloads./setup.shwill setup everything needed for Winpayloads- Start Winpayloads
./Winpayloads.py - Type ‘help’ or ‘?’ to get a detailed help page
You can download Winpayloads here:
Or read more here.
