The latest splash has been made by the Petya or NotPetya Ransomware that exploded in Ukraine and is infecting companies all over the World. It’s getting some people in deep trouble as there’s no way to recover the files once encrypted.
The malware seems to be trying to hide its intent as it doesn’t really seem to be about making money, $300 is a pretty low amount and they setup a very poor mechanism for collecting the money (the Posteo account they used has been shut down).
It is now increasingly clear that the global outbreak of a file-scrambling software nasty targeting Microsoft Windows PCs was designed not to line the pockets of criminals, but spread merry mayhem.
The malware, dubbed NotPetya because it masquerades as the Petya ransomware, exploded across the world on Tuesday, taking out businesses from shipping ports and supermarkets to ad agencies and law firms. Once inside a corporate network, this well-oiled destructive program worms its way from computer to computer, encrypting the infected machines’ filesystems.
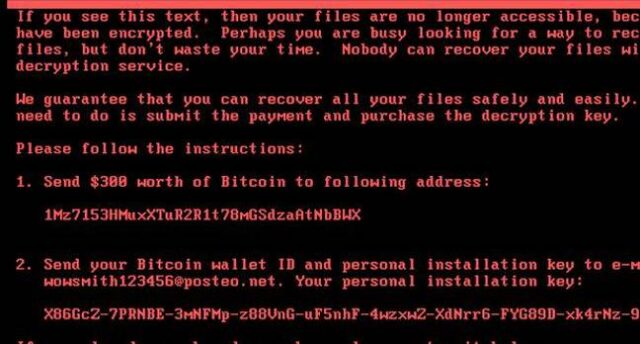
Although it demands about $300 in Bitcoin to unscramble the hostage data, the mechanisms put in place to collect this money from victims quickly disintegrated. Despite the slick programming behind the fast-spreading malware, little effort or thought was put into pocketing the loot, it appears.
At the current value of Bitcoin there’s around $10,000 USD in the wallet mentioned, but with the e-mail address down there’s no way for the victims to get in contact with the bad guys to decrypt their files.
It’s quite probably a nation state attack aimed at the Ukraine, and it just happened to spread outside. It also doesn’t spread over the Internet like WannaCry but only over the local network.
So far, the vast majority of infections have occurred in Ukraine and Russia, but some big names in the West have also suffered. International advertising conglomerate WPP was taken offline (even its website was down), global law firm DLA Piper was infected and, most worryingly, shipping goliath Maersk is warning of a worldwide outage that could seriously bork the global transport supply chain. Computer terminals in major ports were borked for hours by the malware.
In Ukraine itself, which appears to be ground zero for the attack, the situation was critical. Large numbers of businesses were caught by the software nasty – the contagion has broken the automatic radiation monitoring systems in Chernobyl, meaning some unlucky scientists are going to have to take readings manually for the time being. Energy companies were hit as well as government agencies.
According to Ukraine’s cyber-cops, as well as phishing emails booby-trapped with malware-laden attachments, financial software firm MeDoc was used to infect computers in the ex-Soviet nation. We’re told miscreants managed to compromise a software update for the biz’s products, which are widely used in the country, so that when it was downloadable and installed by victims it contaminated their network with NotPetya. If this software was running with domain admin access, it would be immediately game over.
It seems to be using a whole bunch of tech with bits we’ve posted about like Mimikatz and the NSA leak (a modified version of EternalBlue).
It’s definitely some pretty slick coding and an impressive piece of malware. But why it’s been unleashed? We’re unlikely to find out unfortunately.
Source: The Register
