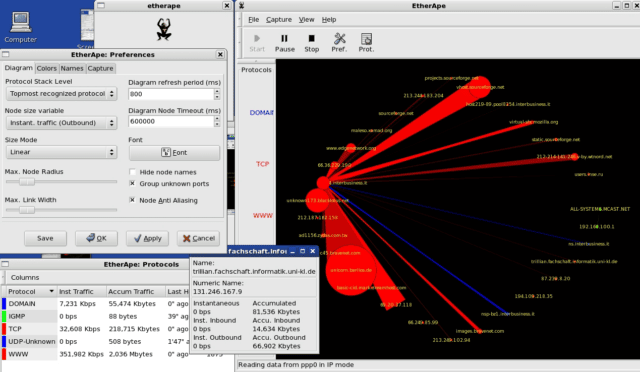
EtherApe is a graphical network monitor for Unix modelled after etherman. Featuring link layer, IP and TCP modes, it displays network activity graphically. Hosts and links change in size with traffic. Colour coded protocols display.
It supports Ethernet, FDDI, Token Ring, ISDN, PPP, SLIP and WLAN devices, plus several encapsulation formats. It can filter traffic to be shown and can read packets from a file as well as live from the network.
Plug it into the management or span port of your switch and get a real-time graphical flow of what’s going on in your network.
Features of EtherApe Graphical Network Monitor
- Network traffic is displayed graphically. The more “talkative” a node is, the bigger its representation.
- Node and link color shows the most used protocol.
- User may select what level of the protocol stack to concentrate on.
- You may either look at traffic within your network, end to end IP, or even port to port TCP.
- Data can be captured “off the wire” from a live network connection, or read from a tcpdump capture file.
- Live data can be read from ethernet, FDDI, PPP, SLIP and WLAN interfaces, plus several other incapsulated formats (e.g. Linux cooked, PPI).
- The following frame and packet types are currently supported: ETH_II, 802.2, 803.3, IP, IPv6, ARP, X25L3, REVARP, ATALK, AARP, IPX, VINES, TRAIN, LOOP, VLAN, ICMP, IGMP, GGP, IPIP, TCP, EGP, PUP, UDP, IDP, TP, ROUTING, RSVP, GRE, ESP, AH, EON, VINES, EIGRP, OSPF, ENCAP, PIM, IPCOMP, VRRP; and most TCP and UDP services, like TELNET, FTP, HTTP, POP3, NNTP, NETBIOS, IRC, DOMAIN, SNMP, etc.
- Data display can be refined using a network filter using pcap syntax.
- Display averaging and node persistence times are fully configurable.
- Name resolution is done using standard libc functions, thus supporting DNS, hosts file, etc.
- Clicking on a node/link opens a detail dialog showing protocol breakdown and other traffic statistics.
- Protocol summary dialog shows global traffic statistics by protocol.
- Node summary dialog shows traffic statistics by node.
- Node statistics export to XML file.
- A single node can be centered on the display and several user-choosen nodes can be arranged in a inner circle with other nodes around.
- An alternative display mode arranges nodes in “columns”.
- Scrollkeeper/rarian-compatible manual integrated with yelp.
Requirements of Etherape
Before you download Etherape Graphical Network Monitor, you may want to verify that the following packages are installed on your system — they are required in order to compile:
- The libpcap packet capture library, available from the Lawrence Berkeley National Laboratory.
- GTK+, available from the GTK+ site. Version 2.12 or above is needed.
- Libglade 2, available from ftp://ftp.gnome.org/pub/GNOME/sources/libglade
- Gnome, available from the Gnome site. Version 2 is needed.
- The standard resolver library (exact name varies with OS and distribution)
There are other tools related to network monitoring you can check out like:
– PBNJ – Network Architecture Monitoring Tool
– The Dude – Automatic Network Discovery & Layout Tool
– Bro – Passive Open-Source Network Traffic Analyzer
You can download Etherape here:
Or read more here.
