For those not familiar before we get to the Telegram DDoS attack, Telegram is an instant messaging system focusing on privacy and multi-platform availability. It was launched by the founders of VK, the largest social network in Russia and is run as an independent non-profit company in Germany.
The client code is open-source and audited and various implementations can be found by various individuals based on the API.
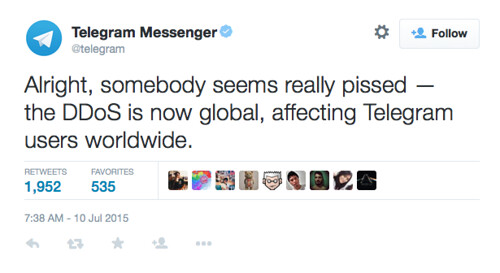
Just a few days ago, users in South East Asia were having difficulty accessing the service and Telegram announced they were suffering a huge DDoS attack.
Popular messaging platform Telegram has been hit with a 200Gbps distributed denial of service (DDoS) attack.
The Tsunami TCP SYN flood kicked off on Friday and hurt users in Asia, Australia, and Oceania, knocking out the service for some five percent of the company’s 60 million active users it has gained in 18 months.
It is a new form of DDoS attack discovered October by Radware security folk who say it is different from regular SYN floods in that it transmits large 100 byte packet sizes about double the regular 40 to 60 byte size.
That Radware says defeats many defense algorithms and quickly consumes bandwidth making even a modest attack clock some four to five gigabits per second.
It seems to be a slight variation of the regular SYN flood with a larger packet size that quickly consumes network resources.
With a 100,000 nodes involved the attack generating over 200GBps of bandwidth – it’s a fairly substantial attack.
The garbage traffic came from about a hundred thousand infected servers, most noticeably, in LeaseWeb B.V., Hetzner Online AG, PlusServer AG, NFOrce Entertainment BV, Amazon and Comcast networks,” Telegram says.
“That said, the attack was distributed evenly across thousands of hosts and none contributed more than five percent of the total volume … by now we know that the attack is being coordinated from East Asia.
“Attacks on the scale of the one we‘re facing today have become possible only recently and it’s the first time we‘ve met anything like this.”
The company says it did not want to discuss its mitigation measures in the event that it could give pointers to attackers unknown.
“Our sysadmin cyborgs are working on this 24 hours a day.”
The attack follows a bizarre smaller DDoS that followed a move by the company to introduce free custom stickers over the service.
It seems like no clear reason why Telegram is the target of this attack, some conspiracy theories claim it to be because of the free custom stickers – which other similar messaging apps make money from.
That seems a little far fetched though, we’ll keep an eye out and see if any more information emerges.
Source: The Register

Roman says
Telegram is considered to be “safe” from peeking by governments and other 3rd parties. East Asia – probably North Korea or China wanted to prevent their citizens at least temporarily from using the messaging service.
moemon xi says
Are there still people using Telegram?! All of my contacts have switched to Threema by now.
Darknet says
Not sure where you’re from, but yah, it’s still pretty huge in Asia. And from my observations, the people using it don’t even know/care it’s security/privacy oriented. It’s just another WhatsApp to them.