Web Security Dojo is a free open-source self-contained web hacking training environment for Web Application Security penetration testing. Tools + Targets = Dojo
What?
Various web application security testing tools and vulnerable web applications were added to a clean install of xubuntu 12.04. Build scripts are available in git at Sourceforge.
Targets include:
- OWASP’s WebGoat
- Google’s Gruyere
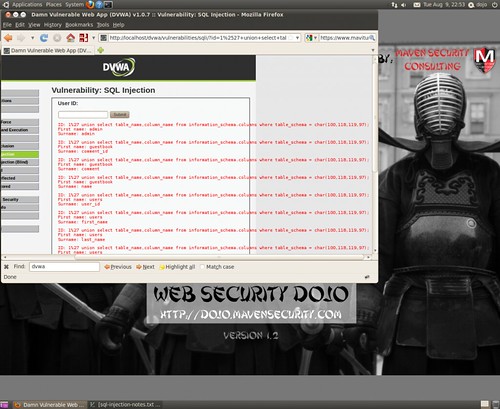
- Damn Vulnerable Web App
- Hacme Casino
- OWASP InsecureWebApp
- w3af’s test website
- Simple training targets by Maven Security (including REST and JSON)
Why?
The Web Security Dojo is for learning and practising web app security testing techniques. It is ideal for self-teaching and skill assessment, as well as training classes and conferences since it does not need a network connection since it contains both tools and targets. Also, this removes the possibility of remote attack on the targets, which are insecure by design. The Dojo contains everything needed to get started – tools, targets, and documentation.
Tools included (starred = new this version):
- Burp Suite (free version)
- w3af
- SQLmap
- Arachni *
- Metasploit
- Zed Attack Proxy *
- OWASP Skavenger
- OWASP Dirbuster
- Paros
- Webscarab
- Ratproxy
- skipfish
- websecurify
- davtest
- J-Baah
- JBroFuzz
- Watobo *
- RATS
- Helpful Firefox add-ons
You can download Web Security Dojo v2.0 here:
Or read more here.
