BSQL Hacker is an automated SQL Injection Tool designed to exploit SQL injection vulnerabilities in virtually any database.
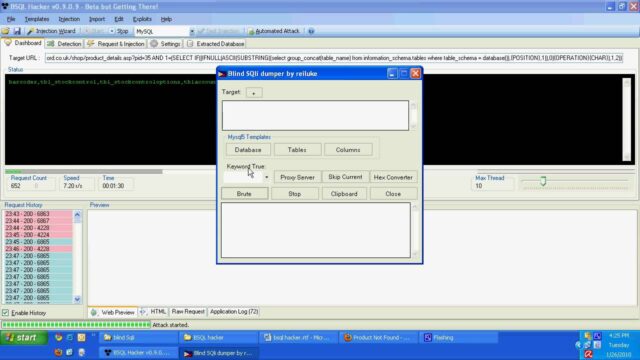
It aims for experienced users as well as beginners who want to automate SQL Injections (especially Blind SQL Injections).
What Can BSQL Hacker Do?
It ships with Automated Attack modules which allows the dumping of whole databases for the following DBMS:
- MS-SQL Server
- ORACLE
- MySQL (experimental)
Attack Templates for:
- MS Access
- MySQL
- ORACLE
- PostgreSQL
- MS-SQL Server
Also, you can write your own attack template for any other database as well (see the manual for details). New attack templates and exploits for a specific web application can be shared via Exploit Repository.
BSQL Hacker Blind SQL Injection Tool Features
- Easy Mode
- SQL Injection Wizard
- Automated Attack Support (database dump)
- ORACLE
- MSSQL
- MySQL (experimental)
- General
- Fast and Multithreaded
- 4 Different SQL Injection Support
- Blind SQL Injection
- Time Based Blind SQL Injection
- Deep Blind (based on advanced time delays) SQL Injection
- Error Based SQL Injection
- Can automate most of the new SQL Injection methods those relies on Blind SQL Injection
- RegEx Signature support
- Console and GUI Support
- Load / Save Support
- Token / Nonce / ViewState etc. Support
- Session Sharing Support
- Advanced Configuration Support
- Automated Attack mode, Automatically extract all database schema and data mode
- Update / Exploit Repository Features
- Metasploit alike but exploit repository support
- Allows to save and share SQL Injection exploits
- Supports auto-update
- Custom GUI support for exploits (cookie input, URL input etc.)
- GUI Features
- Load and Save
- Template and Attack File Support (Users can save sessions and share them. Some sections like username, password or cookie in the templates can be show to the user in a GUI)
- Visually view true and false responses as well as full HTML response, including time and stats
- Connection Related
- Proxy Support (Authenticated Proxy Support)
- NTLM, Basic Auth Support, use default credentials of current user/application
- SSL (also invalid certificates) Support
- Custom Header Support
- Injection Points (only one of them or combination)
- Query String
- Post
- HTTP Headers
- Cookies
- Other
- Post Injection data can be stored in a separated file
- XML Output (not stable)
- CSRF protection support
It allows metasploit alike exploit repository to share and update exploits and attack templates.
For automated SQL Injection you can also try:
– Havij Download – Advanced Automated SQL Injection Tool
– The Mole – Automatic SQL Injection SQLi Exploitation Tool
– jSQL – Automatic SQL Injection Tool In Java
– sqlmap Download – Automatic Blind SQL Injection Tool
You can download BSQL Hacker here:
BSQLHackerSetup-0907.exe no longer available
Or read more here.

Yami King says
The tool itself is quite nice -though it still crashes sometimes over here- and can be proven useful in many situations. Especially the template functionality is timeless, not only for novices, but also for many people just trying to be productive.
But there is one thing I dislike about these kinds of products, and it has something to do with the fact I just said the template functionality is timeless… That is, that these tools should not be necessary anymore, especially not since the SQL Injection and it’s relatives (Blind SQL Injection, Deep Blind SQL Injection, etc..) are one of the most discussed and documented (web)application vulnerabilities out there.
SpikyHead says
Ididnt get a chance to check out the tools as yet..
@Yami
I disagree, such tools are still very much needed. especially for security consultants to show the power of sql injection… or for security audits..
as well as for security new bees
Yami King says
@ SpikyHead
You are correct about the fact that these tools can still be useful and even necessary for security consultants and auditers.
But my comment was especially aimed at the fact that there are still a lot of (web)applications vulnerable to SQL Injections, while it is one of the most documented attack around, and this should not be the case.
The following is a bit abstract (maybe a bit too abstract) but I think you’ll get the basic idea of what I meant:
Instead of making tools to test for SQL Injection vulnerabilities, make the application invulnerable to SQL Injections.Though there is a sort of chicken and the egg problem here, since you need to test your application for SQL Injections to prove it is invulnerable, but that’s not the point I wanted to make.
SpikyHead says
@Yami King
I got that now.. yeah, I agree with you on this. preach secure coding day and night. But, the day is still very far away when applications will be invulnerable to such attacks… as still 99% of the developers are more focused towards features and performance on the cost of security issues.
Till that day, these tools will help us earn our bread. ;)