[ad]
So, I guess you guys are wondering who has won the July contest? It was a pretty close call.
As you know we started the Darknet Commenter of the Month Competition on June 1st and it ran for the whole of June, we have just finished the second month of the competition in July and are now in the third, starting today August 1st – Sponsored by GFI.
We are offering some pretty cool prizes like iPods and PSPs, along with cool GFI merchandise like shirts, keyrings and mugs.

Keep up the great comments and high quality interaction, we really enjoy reading your discussions and feedback.
Just to remind you of the added perks, by being one of the top 5 commenter’s you also have your name and chosen link displayed on the sidebar of every page of Darknet, with a high PR5 (close to 6) on most pages (3000+ spidered by Google).
So announcing the winner for July…it’s backbone, very narrowly beating Sandeep Nain!
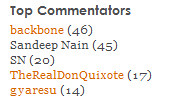
Once again we have to give a shout out to therealdonquixote for his top quality comments in the month of July.
Keep commenting guys, and stand to win a prize for the month of August!
Winner of the month for June was Daniel with 35 comments.

Sandeep Nain says
well thats weird coz.. there were 48 commenst from me and 46 comments from backbone when the contest finished for july month
then how come my comments are reduced by 3…
can’t understand this mathematics
Darknet says
That was at midnight here on July 31st, the contest is according to my time zone because after that I’m asleep so I can’t check.
Sandeep Nain says
if you look at second last comment on this article. you will see my last post for the month was at 11.41PM 31st july. and that was my 48th post. and nobody else posted any comment after that…
so, i am supposed to be the winner with maximum number of posts.
i understand u r the owner/moderator, but competition should end according to the date/time of the server (which is displayed) and not according to your sleep time ;)
Sarah says
Congratulations backbone for being July’s winner! We will be in touch soon to send you the gifts. Keep the comments coming guys, who knows… you might be next month’s winner! In the meantime check out GFI’s latest free whitepaper which explores the PDF spam issue, including how spammers have changed their spamming tactics over the years. Read the PDF spam white paper today – no registration required.
Sandeep Nain says
and moreover it takes only 1 sql query to find the maximum number of posts by 1 person in a given month…
Darknet says
Relax Sandeep, there’s 12 months in a year – I’m sure you can win if you keep up your commenting as you’ve been doing this month.
Remember it’s not simply about quantity aswell as explained, it’s also about quality and consistency – which are taken into consideration.
Like most things in life, in the end everyone gets their just deserts.
Daniel says
Congrats Backbone
backbone says
thanks guys… actually didn’t think I would win, but it seems I got lucky, yeah!
TheRealDonQuixote says
Congrats BKBN!!
Thanks for the shout out DKNT!!
One Love!
Daniel says
therealdonquixote needs to win in august.
TheRealDonQuixote says
Thnx Dan. Alas, its both quantity and quality, that wins the prize. I try to only speak when I have something important to say so that means I don’t write too much ;)
Hey, Darknet, when are you gonna get a forum up in here?
backbone says
TRDQ: check out the affiliates ;) and that should answer the question about the forum…
TheRealDonQuixote says
BackBone: I meant a forum just for Darknet readers. That affiliate link isn’t just for us Darknet lovers. Silly.
backbone says
but just think about it? would you like every day to read a topic that “how do I hack yahoo/gmail/etc”, because I’ve you would have read older articles, you would have seen stuff like this. Or maybe I am wrong and many commenter’s have grown up XD
TheRealDonQuixote says
BKBN – Yeah you have a point, but if the Darknet Forum was via registration (not like the comment areas on the posts, a whole seperate subdomain or something) then there could be a simple test to see if one was knowledgeable enough to be able to register. Like how you used to start that one war game “Mod-X”, only the little tests would have to be randomized or the answers would be all over the net.