[ad]
PRIAMOS is a powerful SQL Injector & Scanner
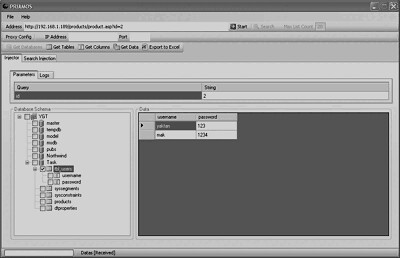
You can search for SQL Injection vulnerabilities and inject vulnerable string to get all Database names, Tables and Column data with the injector module.
You should only use PRIAMOS to test the security vulnerabilities of your own web applications (obviously).
The first release of PRIAMOS contain only SQL Server Database module.
You can watch a demo video here and find out more here:
http://www.priamos-project.com/
If you want something to test you can create your own local vulnerable test platform using this script:
Download Vulnerable ASP page and Database script
You can download PRIAMOS here:
Do try it out and let us know what you think, it’s a new tool but I think it has some promise.

Daniel says
downloading, will play with it tomorrow.
looks interesting. i love gui apps
moOg says
Hum, this article was already posted in april no ?
Why posting it again, the soft is in the same version as in the previous article, and it seems not contain evolutions ?
(ps : sorry for my english :p)
Darknet says
moOg: You are right! Actually I had a feeling I’d posted it before, but then I made a search for PRIAMOS and nothing showed up. I must have typed it wrongly. I’ll consolidate the two articles.
Daniel says
duh, shoulda noticed that
*bangs his head*
backbone says
don’t be harsh with him =)… people make mistakes, the same way that computers do …
I need says
hi, this is a very great software i have used it before then only problem with this software is i can find the sites tht have the sql as a backbone, i had a list now i have lost it can u help me with it ?.
Thank You.